After a first appearance at the Black Hat security conference in 2012 that can only be described as ‘meh’, Apple's head of security engineering and architecture, Ivan Krstić, took the stage a few years later to both announce Apple's bug bounty program (which surprised many security experts) and to reveal Apple's efforts to build a system that effectively prevents them from accessing user data in iCloud. Read More…
After a first appearance at the Black Hat security conference in 2012 that can only be described as ‘meh’, Apple's head of security engineering and architecture, Ivan Krstić, took the stage a few years later to both announce Apple's bug bounty program (which surprised many security experts) and to reveal Apple's efforts to build a system that effectively prevents them from accessing user data in iCloud. Read More…
Password Managers Articles
Using Keyboard Acoustics to Crack Passwords
Plugging a high-performance mechanical keyboard into a laptop may speed up your typing, but there’s one thing to bear in mind. One of the key selling points of these types of keyboards – the acoustic feedback – can give away sensitive data. Yup, you are reading that right: it is possible to sniff out internet banking credentials just by listening to the keyboard's acoustics. Read More…
Project Mirror: The Dashlane Way of Killing the Password
 There is no internet user in this world that hasn’t experienced the constant struggle that is keeping our online identities safe. Some people say the traditional approach is the best (i.e. keeping a password logbook), while others save passwords and other credentials to their browser. And, of course, let’s not forget those – including ourselves – who recommend the use of password management software for the most secure method.
There is no internet user in this world that hasn’t experienced the constant struggle that is keeping our online identities safe. Some people say the traditional approach is the best (i.e. keeping a password logbook), while others save passwords and other credentials to their browser. And, of course, let’s not forget those – including ourselves – who recommend the use of password management software for the most secure method.
In seeing the constant evolution of these solutions, it’s safe to assume that sooner or later there will become a time when internet users can indeed surf the web and keep their most sensitive data safe without the need to remember all those complex passwords that we are often required to create every time. And with Dashlane’s latest project, Project Mirror, this dream is about to become reality. Read More…
How to Protect Yourself from Shoulder Surfing
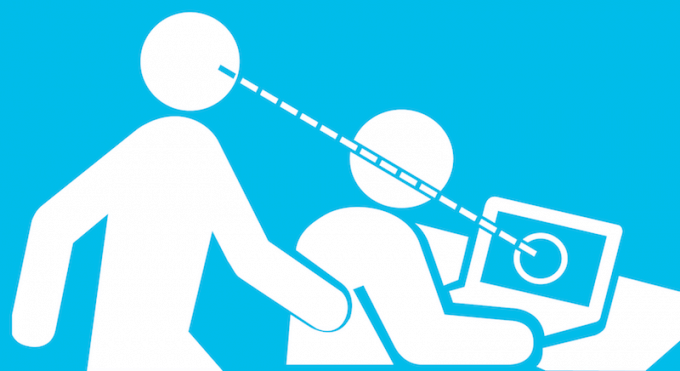
It’s a little frustrating to think that all this effort at protecting your digital life could easily be undone by having someone simply stare over your shoulder and directly observe your personal information. Termed ‘shoulder surfing’, this is particularly effective in crowded places with little privacy, where it is relatively easy to eavesdrop on someone as they enter passwords on their mobile phone or computer. Just think about the sorts of public places you often access social media accounts or enter in bank details and you might, rightfully, start to worry about this potential threat… Read More…
Smart Textile: The Next Step in Password Evolution
 There’s always some new invention to ponder these days, and with technology advancing at such an incredible pace there are new concepts and ideas to consider every day – some more unusual than others. They infect every industry, and password management is no different. While we’re on the brink of new technologies – like facial and voice recognition – we’re even seeing the likes of iris or retina scanning that could end up replacing passwords.
There’s always some new invention to ponder these days, and with technology advancing at such an incredible pace there are new concepts and ideas to consider every day – some more unusual than others. They infect every industry, and password management is no different. While we’re on the brink of new technologies – like facial and voice recognition – we’re even seeing the likes of iris or retina scanning that could end up replacing passwords.
A few years ago all these alternative passcodes would have seemed like they were taken out of a sci-fi novel, but this latest addition to the ever-growing list of authentication methods – the smart textile – is kookier than all of them. It’s safe to say that the future is right upon us. Read More…
The Different Types of Password Cracking Techniques
 Humans are considered the weakest link when it comes to data security – and there’s a solid reason for this. Many people still underestimate the ease with which hackers can crack weak passwords, putting sensitive information at risk. It is vital to understand the importance of having a strong password and how to avoid mistakes that can lead to threats and breaches. Read More…
Humans are considered the weakest link when it comes to data security – and there’s a solid reason for this. Many people still underestimate the ease with which hackers can crack weak passwords, putting sensitive information at risk. It is vital to understand the importance of having a strong password and how to avoid mistakes that can lead to threats and breaches. Read More…
Clever Password Organizer Ideas
 It's amazing how careless people are with passwords: the vast majority of users expose themselves to online theft by ignoring the recommended security measures, according to a study from Cyber Streetwise. The problem with this is that hackers need to compromise only one email address and they can then impersonate the user’s entire digital life. Have you read those horror stories of people waking up to an empty bank account and $30,000 worth of merchandise being shipped to Africa? In the end this is what you expose yourself to if you don’t take online security seriously. Read More…
It's amazing how careless people are with passwords: the vast majority of users expose themselves to online theft by ignoring the recommended security measures, according to a study from Cyber Streetwise. The problem with this is that hackers need to compromise only one email address and they can then impersonate the user’s entire digital life. Have you read those horror stories of people waking up to an empty bank account and $30,000 worth of merchandise being shipped to Africa? In the end this is what you expose yourself to if you don’t take online security seriously. Read More…
Voice Passwords: The Strongest ID Protection Method?
 We all have our own opinion about passwords, but no one could deny the fact that without them our online life would be destroyed by criminals in a millisecond. And it seems the days of memorizing a random set of characters for each and every site and device we ever accessed will soon be gone thanks to clever alternative authentication options like biometric identification.
We all have our own opinion about passwords, but no one could deny the fact that without them our online life would be destroyed by criminals in a millisecond. And it seems the days of memorizing a random set of characters for each and every site and device we ever accessed will soon be gone thanks to clever alternative authentication options like biometric identification.
In fact, the latest smartphone, tablet and laptop generations are always upping the ante, whether that’s by including fingerprint scanning, iris recognition, or facial ID – slowly making the need for strong passwords obsolete.
But there is one solution that is not quite as quite widespread as the above methods: voice passwords. Read More…
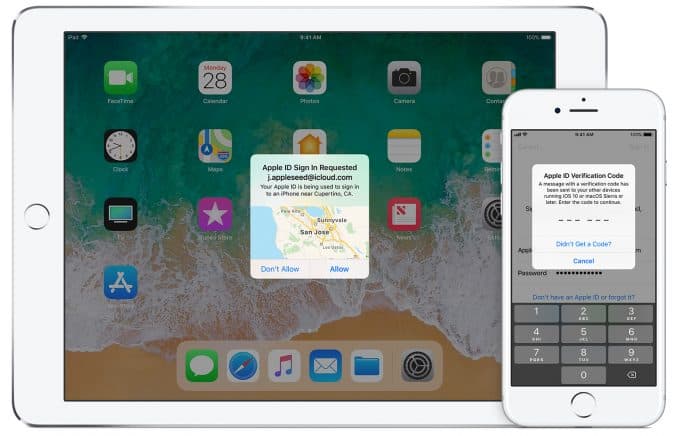
Two-Factor Authentication (2FA) vs Two-Step Verification (2SV) on Apple Devices
If you really want to stay protected while browsing the internet, it’s of utmost importance to beef up your security with as many options as possible. For example, it's highly recommended to use two-factor authentication (2FA) everywhere it is available, but there is also another verification known as two-step verification (2SV). At first glance these two terms may seem to be the same thing, and some ‘experts’ are using the two as interchangeable terms – but there is an important difference between them. Read More…
How to Find All Passwords Used on Your Computer With a Keylogger
A handful of Scandinavian bank Nordea clients had their checking accounts emptied following a phishing scam, the total damage counting more than $1 million and making this case one of the biggest incidents of keylogging yet. Read More…
- « Previous Page
- 1
- …
- 9
- 10
- 11
- 12
- 13
- …
- 16
- Next Page »