Although it was expected to happen years ago, the death of the password is still nothing more than a rumor. Passwords and passcodes are still pivotal elements of user authentication, so the question is not whether passwords will stick around but instead how service providers can get authentication right. Read More…
Password Managers Articles
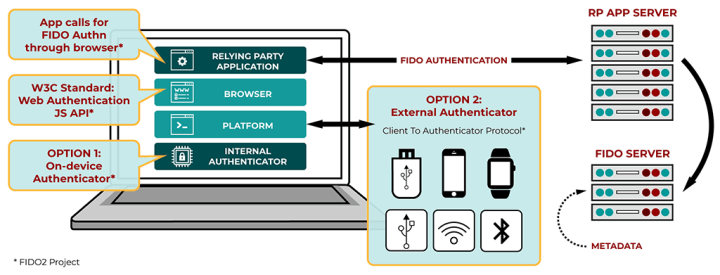
How Does WebAuthn Compare to Passwords?
Have you ever dreamed of a password-free future? A new standard called WebAuthn (short for Web Authentication) seeks to deliver just that by using a combination of offline and online authentication that allows internet users to register and authenticate themselves on the web using various authenticators.
The new proposed standard aims high with its goals: to replace the legacy approach of using a username and password for authentication with today's modern technology. Read More…
When Is It Safe to Enter Your Password?
The sad truth is the internet is a place where cyber criminals are after your money. Yes, by accessing this article you must be connected to the internet and therefore you are likely enjoying the benefits of a connected world, but the bad guys can't wait to catch their next victim.
But it's not exactly news that people want to trick one another for the same old thing: cold, hard, cash. What has changed over time is the tactics that are being used. Nowadays, with the high adoption of the internet and the rise of online shopping and banking, there is a noticeable uptick in phishing scams. Read More…
Tricks to Help You Store and Remember to Use Gift Cards
 If you’re one of those people who gets gifted an abundance of cards, then you could well have hundreds of dollars' worth of cards. As the inventory of gift cards grows, managing them becomes a challenge, and risky, too, because they are like cash: they cannot be replaced if they are stolen.
If you’re one of those people who gets gifted an abundance of cards, then you could well have hundreds of dollars' worth of cards. As the inventory of gift cards grows, managing them becomes a challenge, and risky, too, because they are like cash: they cannot be replaced if they are stolen.
The typical situation with gift cards shows that if they're not used within the first three to six months of being activated, then they just end up adding to the billion-dollar amount of unspent gift cards. So how can you make the most of your gift and loyalty cards? Here are some tips to keep onto them and to help you avoid wasting a great opportunity to use them. Read More…
The Importance of BIOS Passwords in Windows 10
 Despite the fact that most users still have issues with creating strong yet memorable passwords, they are at least aware of the importance of properly securing their computers. And thanks to the inclusion of biometric authentication methods like scanning a fingerprint, setting up an extra layer of security can be done in mere seconds.
Despite the fact that most users still have issues with creating strong yet memorable passwords, they are at least aware of the importance of properly securing their computers. And thanks to the inclusion of biometric authentication methods like scanning a fingerprint, setting up an extra layer of security can be done in mere seconds.
Still, even if the computer does provide advanced authentication options, wrongdoers can easily bypass the user account’s login screen without the need to crack a single password by accessing sensitive files and data through the PC’s BIOS. However, this scenario can be prevented by creating a BIOS password, the computer’s first line of defense that locks any unauthorized users out even before the system is booted up. Read More…
Emoji Passwords: Can’t Crack This :)
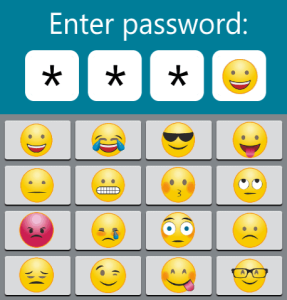 We are constantly told that passwords are useful as they are help to protect our most sensitive personal information. Admittedly, that’s true; but just ask the average user about passwords and it’s guaranteed that they’ll complain about how tedious it is to create long and complex login credentials for all those accounts. And if that’s not enough, there is the issue of actually memorizing those passwords that, let’s face it, is downright impossible without the help of the right tools like a password manager. So, it’s not surprising that people are looking for alternatives whenever possible, whether that’s biometric authentication, a pattern or anything but a password.
We are constantly told that passwords are useful as they are help to protect our most sensitive personal information. Admittedly, that’s true; but just ask the average user about passwords and it’s guaranteed that they’ll complain about how tedious it is to create long and complex login credentials for all those accounts. And if that’s not enough, there is the issue of actually memorizing those passwords that, let’s face it, is downright impossible without the help of the right tools like a password manager. So, it’s not surprising that people are looking for alternatives whenever possible, whether that’s biometric authentication, a pattern or anything but a password.
However, a few years ago a new contender, the emoji password, appeared with the hopes of changing what we think of a password today. Now the question is: do emoji passcodes have the potential to replace their regular counterparts and finally put an end to the forced use of those annoying complex passwords? Read More…
How Does Password Hashing Protect My Passwords?
Have you ever tried to recover the password to a web-based service and all you received via email was a temporary password or a link with instructions to reset the password? If that happened, then this is a good sign, because it means that the service doesn't store your password in a vulnerable database and uses what is called ‘password hashing’ instead. Read More…
How to Protect Your Digital Gaming Self
 Playing games online is a great way to let out some steam after a long, exhausting day of work or to just have fun with friends and fellow gamers. And honestly, who doesn’t want to escape reality for a while and enter a world full of so many opportunities and countless hours of entertainment? In fact, most gamers are so eager to play their favorite online games that they often forget to properly protect their accounts from being hacked.
Playing games online is a great way to let out some steam after a long, exhausting day of work or to just have fun with friends and fellow gamers. And honestly, who doesn’t want to escape reality for a while and enter a world full of so many opportunities and countless hours of entertainment? In fact, most gamers are so eager to play their favorite online games that they often forget to properly protect their accounts from being hacked.
However, if that account isn’t enforced with a strong password, then there is nothing to stop your most sensitive data from ending up in the hands of nefarious sorts on the dark web. Thankfully, making a gaming account completely hacker-proof is just as easy as hitting “Start” on the main screen. Read More…
Remembering Passwords With Hypnosis
 Even though there are many alternatives to passwords – just look at the constantly-evolving biometric authentication – security experts still consider passwords to be the most effective method of protecting highly sensitive personal data from getting stolen. Despite the safety that they can bring, though, users still hate passwords, especially those that are hard to memorize due to their complexity.
Even though there are many alternatives to passwords – just look at the constantly-evolving biometric authentication – security experts still consider passwords to be the most effective method of protecting highly sensitive personal data from getting stolen. Despite the safety that they can bring, though, users still hate passwords, especially those that are hard to memorize due to their complexity.
However, it doesn’t matter whether the password is strong or not, if it’s forgotten for whatever reason, then you can basically say goodbye to that password forever and, with it, the account that it belongs to. But that doesn’t have to be the case because, as it turns out, the human brain can store many things in the subconscious, including seemingly forgotten passwords. All that’s needed to recover this lost info is hypnosis, the therapeutic method often used to enhance the memory and hopefully to help that password resurface from the depths of the mind. Read More…
5 Tips for Safeguarding Your USB Drive
 USB thumb drives are appearing with higher and higher storage capacities, and as such they have become the preferred tools for offline and portable data storage. The small form factor and portability also means pen drives are quite easily lost, and so the data stored on them might land in the wrong hands and end up used for malicious purposes. Read More…
USB thumb drives are appearing with higher and higher storage capacities, and as such they have become the preferred tools for offline and portable data storage. The small form factor and portability also means pen drives are quite easily lost, and so the data stored on them might land in the wrong hands and end up used for malicious purposes. Read More…
- « Previous Page
- 1
- …
- 5
- 6
- 7
- 8
- 9
- …
- 16
- Next Page »