 Have you been getting missed phone calls from weird numbers at suspicious times of the day? Or have you received weird messages from unknown phone numbers claiming that they represent companies or services that you use and trust? Whatever you do, don't call those numbers back and take the messages with a grain of salt, as paying them any heed could well make you the next victim of a scam.
Have you been getting missed phone calls from weird numbers at suspicious times of the day? Or have you received weird messages from unknown phone numbers claiming that they represent companies or services that you use and trust? Whatever you do, don't call those numbers back and take the messages with a grain of salt, as paying them any heed could well make you the next victim of a scam.
How Phone Scams Work
It's very easy to fall into the trap of thinking “I have nothing to hide” because most users believe that hackers are only after wealthy people or corporations. The reality is that hackers are opportunistic people who consider anyone to be a potential target. So, it's wise to apply at least the very basic security measures.
SMS Hack
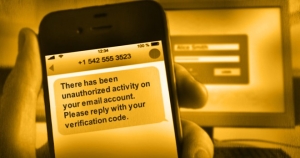
For example, a hacker needs only a user's email address and phone number to break into their email account – even if the account is protected by two-step verification – to take over the digital life connected to that email address. Dubbed ‘password recovery scams’, hackers use the two-step verification method utilized by various email providers to trick users into handing over access to their accounts.
As reported by security firm Symantec, once a hacker knows the target's email address and phone number, they send a message asking them to verify their account by replying with the verification code the email provider sends to the registered phone number. If the target replies with an actual security code, it opens the door for the hacker to reset the password using the one-time code, and as such the rightful user is locked out of their email account.
Voicemail Hack
![]() If you think that voicemail is secure and that no one can mess with it, then you are quite wrong. The FCC is warning users about the existence of a hack that allows cyber criminals to break into a voicemail system with unchanged default or easy-to-guess passwords and use it to make very long international calls.
If you think that voicemail is secure and that no one can mess with it, then you are quite wrong. The FCC is warning users about the existence of a hack that allows cyber criminals to break into a voicemail system with unchanged default or easy-to-guess passwords and use it to make very long international calls.
Apple Support Hack
Scammers don't shy away from acting in the name of any respected company, Apple included. They don't need to break into iCloud to get your username and password, it's enough to simply call you as a supposed Apple Support employee to squeeze the information out of you. The problem with this situation is that Apple Support will never ask for your Apple ID and/or password. If this does happen, then you can be sure that there is a scammer on the other end of the line that is after your money. The best thing anyone can do in this situation is to save the number, hang up the phone and report the situation to Apple.
Cell Phone Porting Scam Leads to Identity Theft
A nightmare can easily start with just a text message from the cell carrier saying “your password has been changed”. We are pretty sure that no one wants to wake up to the “surprise” message that many T-Mobile customers have experienced where they had their phone number ported and their lives ruined after a number of unauthorized transfers of money from their bank accounts.
What Can Users Do to Protect Themselves?
 As always, be sure to apply at least the bare minimum of available security measures. When it comes to phone scams the least you can do is to not call the unusual phone numbers back because you could well wake up to a hefty phone bill.
As always, be sure to apply at least the bare minimum of available security measures. When it comes to phone scams the least you can do is to not call the unusual phone numbers back because you could well wake up to a hefty phone bill.
Of course, SMS messaging is still used by banks as a means of communication. If possible, it’s better to stop using text messages as the second factor in the authentication process. The NIST has already deprecated the use of SMS for 2FA but banks are slow to move forward to more secure systems such as software or hardware tokens.
Alongside good password hygiene – in other words using a unique and cryptographically secure password for every account created both online and offline with the help of a password manager – it’s also good to think twice before clicking on a link in an email or text message, asking yourself two questions before doing so:
- Is the sender legitimate?
- Were you expecting an email/text message containing a download link or one-time password?
If the answer to either question is ‘no’, then it is likely you are the target of a phishing scam and as such it's wise to avoid downloading the attachment or clicking on the link in the email or text message.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
Get the Best Deals on Password Managers
Subscribe to our monthly newsletter to get the best deals, free trials and discounts on password managers.

Share Your Comment