 Employees today need to access several different accounts throughout their daily activities, and it's vital that the associated passwords are strong and secured to prevent data breaches. But how can employees be expected to remember lengthy and random passwords for all their logins? Hopefully, it’s already widely known that keeping passwords on sticky notes is a big no-no. Organizations should instead be using password managers, which are an easy way to maintain all necessary credentials stored safely in a vault protected by a master password.
Employees today need to access several different accounts throughout their daily activities, and it's vital that the associated passwords are strong and secured to prevent data breaches. But how can employees be expected to remember lengthy and random passwords for all their logins? Hopefully, it’s already widely known that keeping passwords on sticky notes is a big no-no. Organizations should instead be using password managers, which are an easy way to maintain all necessary credentials stored safely in a vault protected by a master password.
However, this introduces another problem: organizing the password manager accounts. While this may not be a problem for startups or small businesses, it's clear that the larger a company becomes, the harder it gets to create and revoke employee access. That's why SCIM APIs were created – to provide IT administrators with the ability to manage their organization’s network and its users from an admin console. The most popular SCIM API is the Microsoft Azure Active Directory – also known as AD – which is used by most Fortune 1000 companies. It's no surprise that password managers with business plans provide AD integration allowing companies to easily manage accounts, vaults, and password sharing between employees.
How to Integrate LastPass With Azure Active Directory
Enterprise subscribers have access to the Windows service LastPass Active Directory Connector that can be downloaded from the password manager's Admin Console under Directory integrations. After installing the software outside the domain controller and logging in with the LastPass Enterprise admin email address and master password, you can configure the software.
 LastPassThe Connection tab is where the administrator sets the connection between LastPass and the Active Directory by inserting the domain, credentials, and base DN.
LastPassThe Connection tab is where the administrator sets the connection between LastPass and the Active Directory by inserting the domain, credentials, and base DN.
The Actions tab contains all configurations regarding how to react when specific events occur in the company's Active Directory. Although admins are free to configure the settings as they prefer, it's advisable to disable accounts instead of deleting them to prevent actions against user accounts, such as full vault data loss.
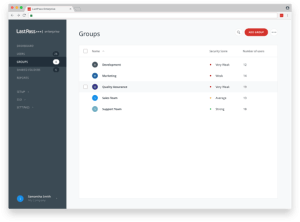
Next, the administrator needs to configure the synchronization settings to specify fields, groups, and users to sync between LastPass and Active Directory. All accounts need to have an email address listed in Active Directory for this to work, and it's possible to filter users based on group membership.
Lastly, the debug tab is where admins can clear the cache and find the log folder for troubleshooting AD Connector syncing issues.
How to Integrate 1Password With Azure Active Directory
1Password also uses a specific application called SCIM bridge to integrate with the Azure Active Directory, but it's a bit more complicated to set up.
 First of all, companies need an OAuth bearer token and an encrypted scimsession file to deploy the SCIM bridge, the location of which can be easily found on 1Password's website. Once the admin has the necessary items, the application can be installed. 1P advises the use of a container, and offers dedicated guides for Google Cloud Platform, Azure Kubernetes Service, and DigitalOcean Kubernetes Service.
First of all, companies need an OAuth bearer token and an encrypted scimsession file to deploy the SCIM bridge, the location of which can be easily found on 1Password's website. Once the admin has the necessary items, the application can be installed. 1P advises the use of a container, and offers dedicated guides for Google Cloud Platform, Azure Kubernetes Service, and DigitalOcean Kubernetes Service.
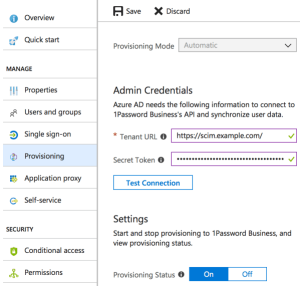
After the installation, administrators need to access their Microsoft Azure account to connect the identity provider to the SCIM bridge. To do so, they need to select ‘Enterprise application' under the ‘Azure Active Directory’ tab in the sidebar, click ‘New application', and click ‘Non-gallery application'. Here, admins can type the display name, select ‘add', and the app is created. To configure the application, the admin has to go to the details page of the 1Password app just created and do the following:
- Click ‘Provisioning' in the sidebar.
- Set ‘Provisioning Mode' to automatic.
- Insert the Tenant URL – where the SCIM bridge was configured – and the 1P OAuth bearer token.
- Set ‘Provisioning Status' to ‘On' and hit ‘Save'.
Organizations that want to sync specific users or groups need to set ‘Scope' to ‘Sync only assigned users and groups', click save, and then manage accesses by clicking on ‘Users and Groups'.
How to Integrate RoboForm With Azure Active Directory
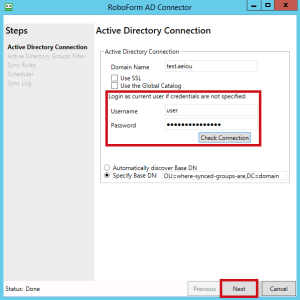 RoboForm also offers AD integration through its RoboForm AD Connector. It can be downloaded from the user creation prompt in the company's administrator console.
RoboForm also offers AD integration through its RoboForm AD Connector. It can be downloaded from the user creation prompt in the company's administrator console.
After installing the program and logging in with RoboForm’s admin account, insert the Active Directory admin credentials and specify the Base DN. The latter can also be left to be discovered automatically by RoboForm.
The next step is to select which of the Active Directory groups should be synced into the RoboForm for Business Company account and go over all the sync rules, which are pretty straightforward to set. The last two steps are to schedule RoboForm's sync period and set the location where the RoboForm AD Client will store its logs.
When everything is done, the admin needs to press ‘Start' so the software begins syncing. If there's a need to change any of the settings, the admin just needs to click ‘Edit Configuration'.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
Get the Best Deals on Password Managers
Subscribe to our monthly newsletter to get the best deals, free trials and discounts on password managers.

Floris says
Thank you for this quick overview.
I think we can conclude that none of these 3 have a real Azure Active Directory SAAS integration😥. As all require downloaded client software to run somewhere.
Also a key functionality to compare, of which I know Roboform has/can provide, is being able to share credentials in a safe way(without needing to provide the password) and being fully webbased functional.
Daniel (Best Reviews Team) says
Hello Floris, and thank you for your comment.
Indeed, all the password managers mentioned in this article require you to download a specific app to integrate with Azure Active Directory. If you’re looking for a password manager that can be configured on Azure Active Directory’s dashboard, we recommend trying out Keeper. It’s also a great password manager, and you can find the app within Azure AD. Have a nice day!