 After a first appearance at the Black Hat security conference in 2012 that can only be described as ‘meh’, Apple's head of security engineering and architecture, Ivan Krstić, took the stage a few years later to both announce Apple's bug bounty program (which surprised many security experts) and to reveal Apple's efforts to build a system that effectively prevents them from accessing user data in iCloud.
After a first appearance at the Black Hat security conference in 2012 that can only be described as ‘meh’, Apple's head of security engineering and architecture, Ivan Krstić, took the stage a few years later to both announce Apple's bug bounty program (which surprised many security experts) and to reveal Apple's efforts to build a system that effectively prevents them from accessing user data in iCloud.
iCloud Keychain
 You may already be using Apple's cloud-based password management service, iCloud Keychain. Apple introduced this service years ago, but, as we have reported, it hasn't always shined when it comes to security. And that's why Apple wasn't eager to talk about it. But things have changed since then, and, as Krstić mentioned on stage, Apple reviews their security measures from time to time to implement better, more secure measures.
You may already be using Apple's cloud-based password management service, iCloud Keychain. Apple introduced this service years ago, but, as we have reported, it hasn't always shined when it comes to security. And that's why Apple wasn't eager to talk about it. But things have changed since then, and, as Krstić mentioned on stage, Apple reviews their security measures from time to time to implement better, more secure measures.
With the latest update, Apple's goals were to develop a ‘shield’ to address various hacking scenarios such as brute-forcing iCloud passwords, hacking Apple's servers, and the risk of inadvertently building a backdoor into their system.
The traditional method for securely synchronizing user passwords and credit card information between users' devices was traditionally done either by securing the vault with a strong randomly-created key (as 1Password does, for example) or protecting data with a key derived from the user's password.
Both approaches have their pros and cons, and, according to Apple, the first approach is cryptographically correct but not user friendly, while the second approach gives privilege to the account provider. In this way it can enable unwanted access to the protected data, so Apple decided to come up with its own method for securing user secrets.
With the goal of having password data available on all Apple devices owned by the user, synchronization protected with strong cryptographic keys, and enabling recovery if a user loses all their devices and locks themselves out from the system, the company has implemented its own method for the iCloud Keychain service.
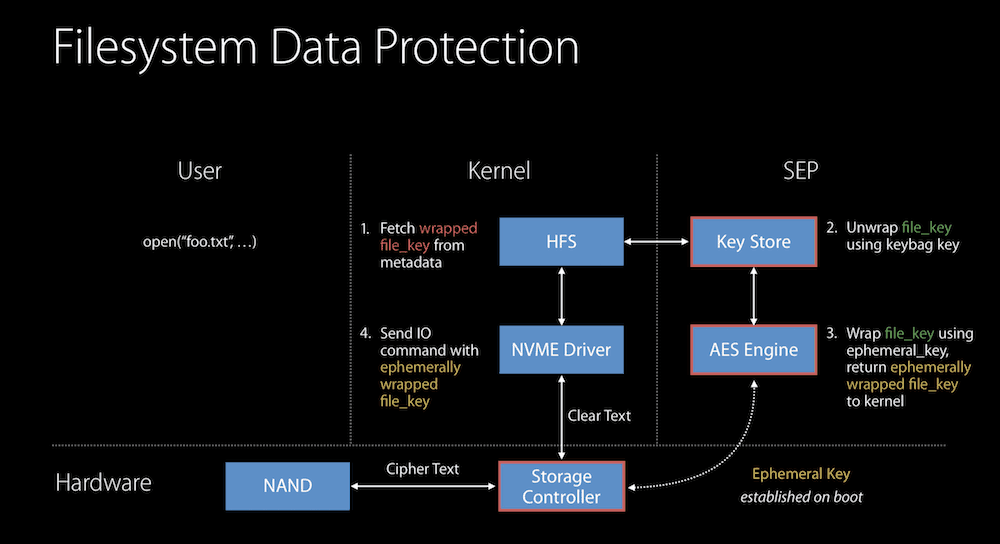
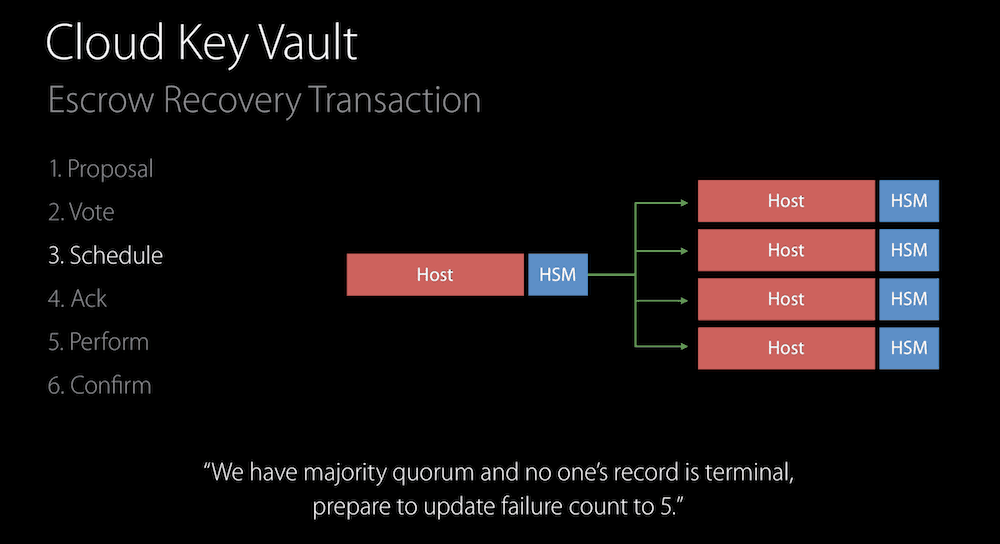
Apple has turned to Hardware Security Modules (HSMs), hardware that stores and operates with cryptographic keys and prevents any guessing attacks. The iPhone secures data using a hardcoded 2048-bit RSA public key and communicates directly with the Apple HSM, which will then decrypt the information. No one else can access the data, not even Apple.
If a user wants to authorize additional devices to use iCloud Keychain or recover the iCloud Keychain data, he or she needs to enter the iCloud Security Code, which is a passcode they enter on a daily basis, and most likely their device passcode. They authenticate themselves using the Secure Remote Password protocol and as a result communicate with the HSM without ever disclosing their data to Apple.
To address brute-force attacks, Apple can protect data by limiting the number of login attempts. In other words, if you don't know the correct passcode, you will be locked out of the account, and in this case not even Apple can help you recover that data.
To address accusations of backdoors into its security system being built – see the FBI's request to develop software that would weaken the security measures implemented in iOS – Apple says it is removing the code-signing keys that reside in the HSM through a process they call “physical one-way hash function”.
As Krstić explained in plain English: “We run the cards through a blender”. Of course, the hashes go through a verification process prior to their destruction, and while the process is not completely ‘foolproof’ it is a measure that other tech companies should follow.
In the end, it all comes down to trust. Apple's head of security stepped on stage to explain the security measures the company takes to continue to earn the trust of more than a billion active users.
The average user is unable to verify these claims, but that will be the job of security experts. And the same people continue to warn Apple if they spot a security vulnerability that weakens the measures the company has taken. Fortunately, so far Apple has been responsive, patching the security flaws it has been notified about.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
Get the Best Deals on Password Managers
Subscribe to our monthly newsletter to get the best deals, free trials and discounts on password managers.

Share Your Comment