Just like all modern software, password managers are all designed to be as convenient as possible for everyone, whether you’re a less tech-savvy user or an IT expert.
Just like all modern software, password managers are all designed to be as convenient as possible for everyone, whether you’re a less tech-savvy user or an IT expert.
Convenience also means that password manager companies try to avoid those particularly fancy terms that not even linguists can decipher.
However, when searching for the ideal password manager solution – either on the internet or by going through our site – you may come across certain terms that cannot be avoided and yet could be confusing or downright incomprehensible for users who have never dealt with password managers before. Understanding these terms is crucial to choosing the best solution possible, which is why we have collected the most common and important expressions related to the world of password manager software.
Terms
AES-256 Bit Encryption
AES-256 is the norm used on almost every website to encrypt highly sensitive data, and is currently one of the most secure encryption methods in existence. AES stands for Advanced Encryption Standard, which is a cipher chosen by the U.S. government to be the standard encryption for securing data online. The ‘256’ relates to the size of the “key” being used, and while this can get complicated essentially it affects what level of encryption data must go through before it is sent to its destination. The bigger the size of the key is the better, since a hacker will have to go through more attempts at cracking the correct combination before successfully deciphering the data. In other words, data on sites protected by AES-256 encryption is virtually impervious to hacking.
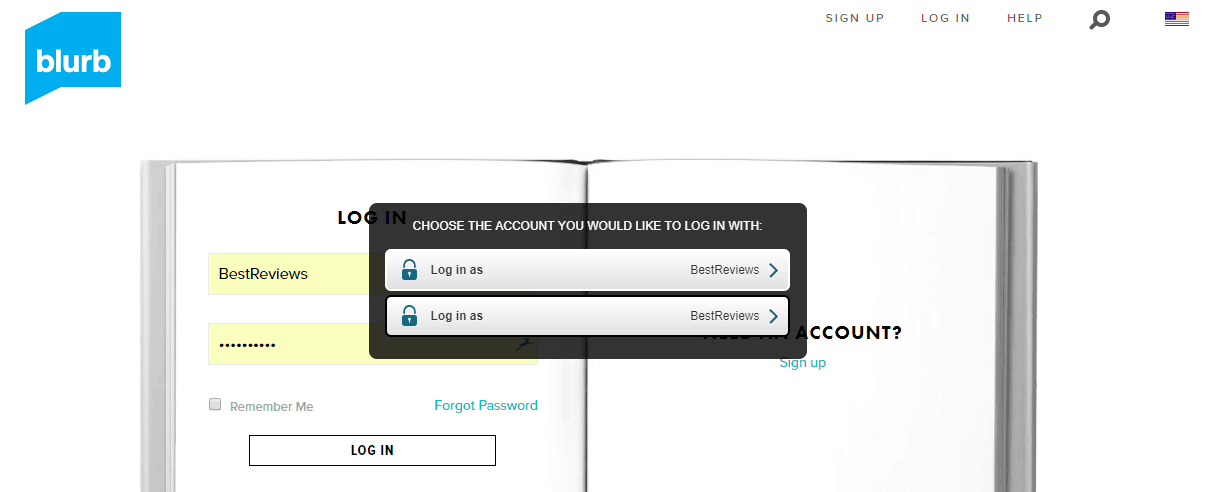
Autofill
A feature provided by password managers and web browsers to reduce the time of filling out boxes on login screens and online forms. Each time you enter your login credentials or fill out a form for the first time this feature will prompt you to save the information to either the browser’s own cache or the password manager’s vault, so next time you visit the same page the program will automatically fill any boxes that are required for accessing a site or completing an online purchase.
Biometric Authentication
Biometric authentication is one of the most secure authentication methods since it relies on the unique biological characteristics of the person it is registered, such as using the human face, fingerprints, voice, or eyes for confirmation. When using biometric authentication the system only permits access to a device or a website if the provided biometric data matches the data stored in the authenticator’s database. Since this technology is available in top-tier smartphones only, password managers always use fingerprint-based biometric authentication as part of the two-factor authentication – meaning it’s necessary to provide both a biometric sample and your password in order to access restricted accounts.
Keylogger
Keylogger – AKA keystroke logger or keyboard capturer – is a device or program that records the keys used on a computer’s or smart device’s keyboard. Although keylogging can be used for studying human-computer interaction – to such an extent that the computer can predict what you’re about the type – it can also be turned into a weapon against innocent users to steal their passwords and other credentials. The best ways to protect yourself against keyloggers is to examine your device for unknown hardware and to use preventive methods such as antivirus and one time passwords.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
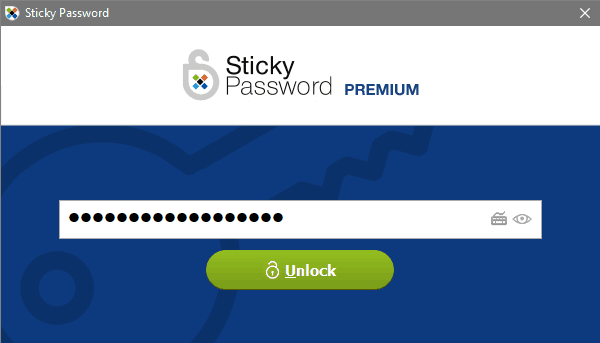
Master Password
The master password is your primary requirement for logging in to your password manager’s vault and accessing all your stored credentials, including passwords. As it is literally ‘the only password you’ll ever need’, it is not only required to be strong but that it remains completely hidden from the password manager’s developer as well. This is due to the fact that recovering your master password should you lose it is virtually impossible and always results in the creation of a new master password.
Offline Database Synchronization
A synchronization method with which devices using the same password manager solution can share the same information without the need to be connected to the internet and be vulnerable to remote hacker attacks. Due to compatibility issues offline syncing only works between computers and requires a USB stick.
One Time Passwords
One time password (OTP for short) is a password generated by a computer algorithm that is valid for only one login session and for a limited period of time. This way hackers are unable to access your account or accounts should your login credentials be stolen. One time passwords can also be used as part of two-step authentication and two-factor authentication alike, or for simply adding a device to a service’s trusted device list (i.e. a password manager’s vault or a Google account).
OpenID
OpenID is an open standard and authentication protocol that allows users to be authenticated by co-operating sites using a third party device. With OpenID ad hoc login systems can be fully eliminated since users can log into multiple (unrelated) websites that accept OpenID authentication without the need to have a separate password for each and every site they are registered to.
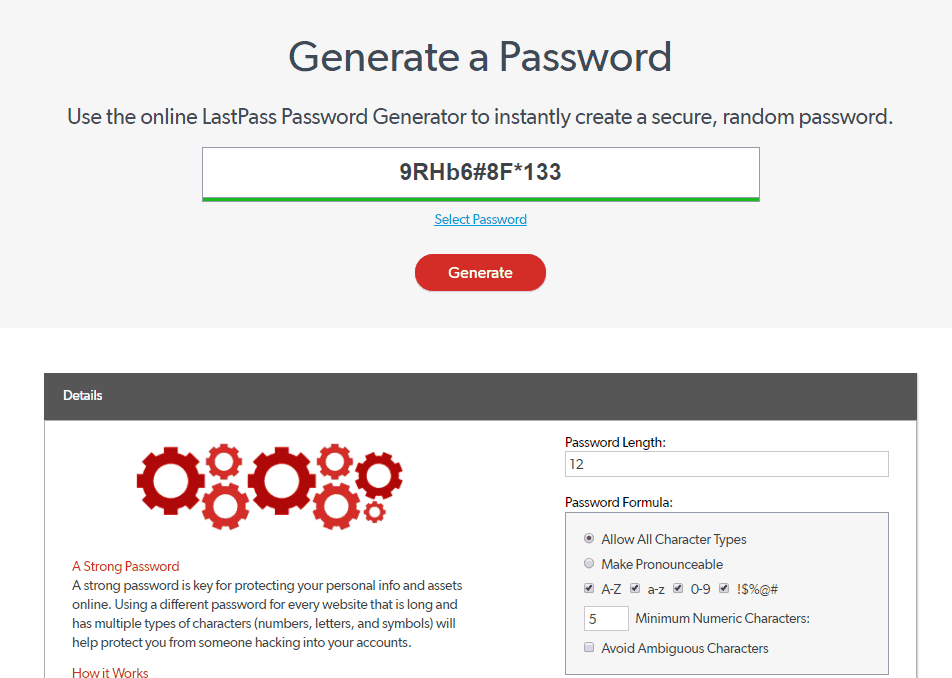
Password Generator
A password generator is a program with which users can generate long and complex passwords within seconds to replace weak login credentials. When using a password generator it is possible to determine how long it should be and whether it should include capital letters, numbers and ambiguous characters. Certain password generators are capable of creating complex passwords that aren’t a string of random numbers, can be read and understand and – most importantly – memorized. Password generators are always included in password managers, but there are plenty of online password generators as well, often provided by password manager companies.
PBKDF2 SHA-256
PBKDF2, or Password-Based Key Derivation Function 2, is an algorithm created to strengthen passwords and therefore make them immune to brute-force attacks. It is usually implemented with the SHA-256 secure hashing algorithm – which is created by the NSA – that generates unique hash values from certain data, encrypting them in such a way they cannot be deciphered by anyone, including the developers of the password manager.
Phishing
Phishing is an attempt by hackers using tricks to obtain sensitive data such as usernames, passwords and other credentials for malicious reasons. Phishing is usually carried out by sending an email or any other form of electronic communication disguised as a message coming from an otherwise trusted entity (such as banks, ISPs, Google, Amazon, Netflix) and typically contain a link that directs the victim to a site that looks similar to the original. However, providing the login credentials at the fake site results in giving up this sensitive data to hackers, meaning the victim involuntarily helps criminals to break into their own accounts.
Phishing attacks are usually easy to notice, since the message with the link is often written in poor English, while the link’s URL will differ from the one used by the site the fake one is pretending to be.
Salted Password Hashing
This has the same meaning as ‘salting the earth’, where the hash itself is used with the password to avoid it ever being used again. This means that before the password is turned into the scrambled representation of itself (hashed) the site storing the password pastes a unique, random string of characters to your password (the salt) and then performs the hashing process. This ensures that if the password matches with the password of another user – like in the case of ‘123456’ or ‘password’ – the added salt prevents hackers from easily decrypting the obtained information.
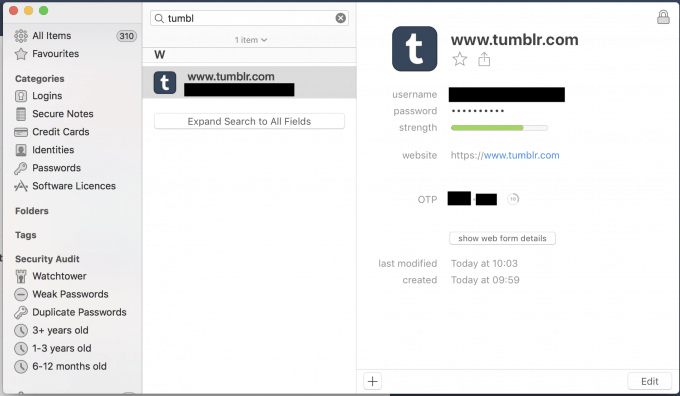
Secure Notes
The term ‘secure notes’ is used as an umbrella term for any type of credential that doesn’t fall into the category of a password: licenses, ID documents, Wi-Fi and internet settings, receipts from online purchases or plain text can all be considered secure notes. All data stored in secure notes is encrypted the same way that passwords are, meaning that anything entered into the password manager’s vault is only known to the user or other trusted parties.
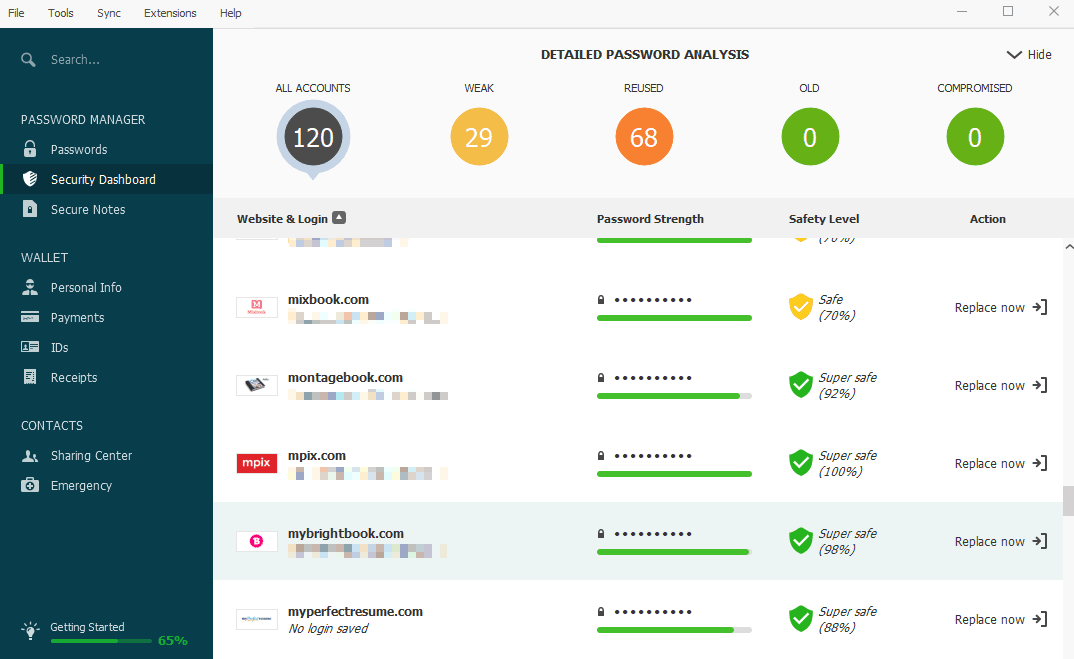
Security Challenge
The security challenge, better known as the password evaluator, is a built-in feature of password managers that examines the strength of all of your passwords and lists those credentials that are deemed to be easily decipherable. The evaluator usually indicates the strength of a password by a color (from red and orange through to yellow and green) or a percentage, and if it finds the password weak it automatically prompts you to change said password to a stronger one.
Security Token
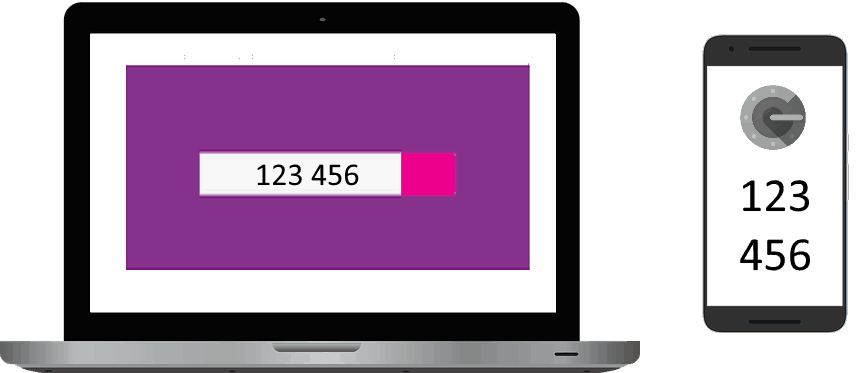
The security token is an electronic device or a built-in feature of two-step authentication apps used to gain access to a resource that is password or PIN-code protected. The device or app can act as the sole method of accessing the protected site or in addition to a password or PIN code. Before the user is able to proceed to the desired account, the security token generates a random string of characters (usually numbers) that, like one time passwords, can be used once and are required to be inserted into the corresponding box in order to finish the login process.
Smart Cards
The term smart card refers to any pocket-sized card containing integrated circuits (usually a microchip) with which it’s capable of personal identification, authentication, data storage and even performing contactless payments (in the cases of credit and debit cards). When used for authentication or personal identification purposes, the card’s PIN number can be used, but certain cards can store an encrypted digital certificate and other relevant information, with which the process becomes even more secure. Due to the nature of this smart cards are usually used as security tokens, forming an integral part of the two-step authentication process.
Two-Factor Authentication
Two-factor authentication – often abbreviated 2FA – is a type of multi-factor authentication (MFA) during which the user accessing a password-protected site has to present two authentication factors in order to access certain data. 2FA usually requires the possession of a password and either a device or an app that generates a security token or is capable of biometric authentication. Although two-factor authentication slows down the login process, it massively reduces the risks of getting your accounts hacked since the attackers have to be in possession of both your password and the device generating the secondary passcode in order to successfully break into your account.
Two-Step Verification
Two-step verification uses the same mechanism as two-factor authentication, yet it is a more primitive predecessor and not really an alternative due to the lack of multiple authentication factors. Unlike 2FA, which uses the combination of a password and a code generated by a secondary device, two-step authentication doesn’t require a secondary device to be able to access the desired site or account. Due to this fact two-step authentication is more vulnerable since the hacker doesn’t have to acquire two factors from you in order to be able to access your accounts.
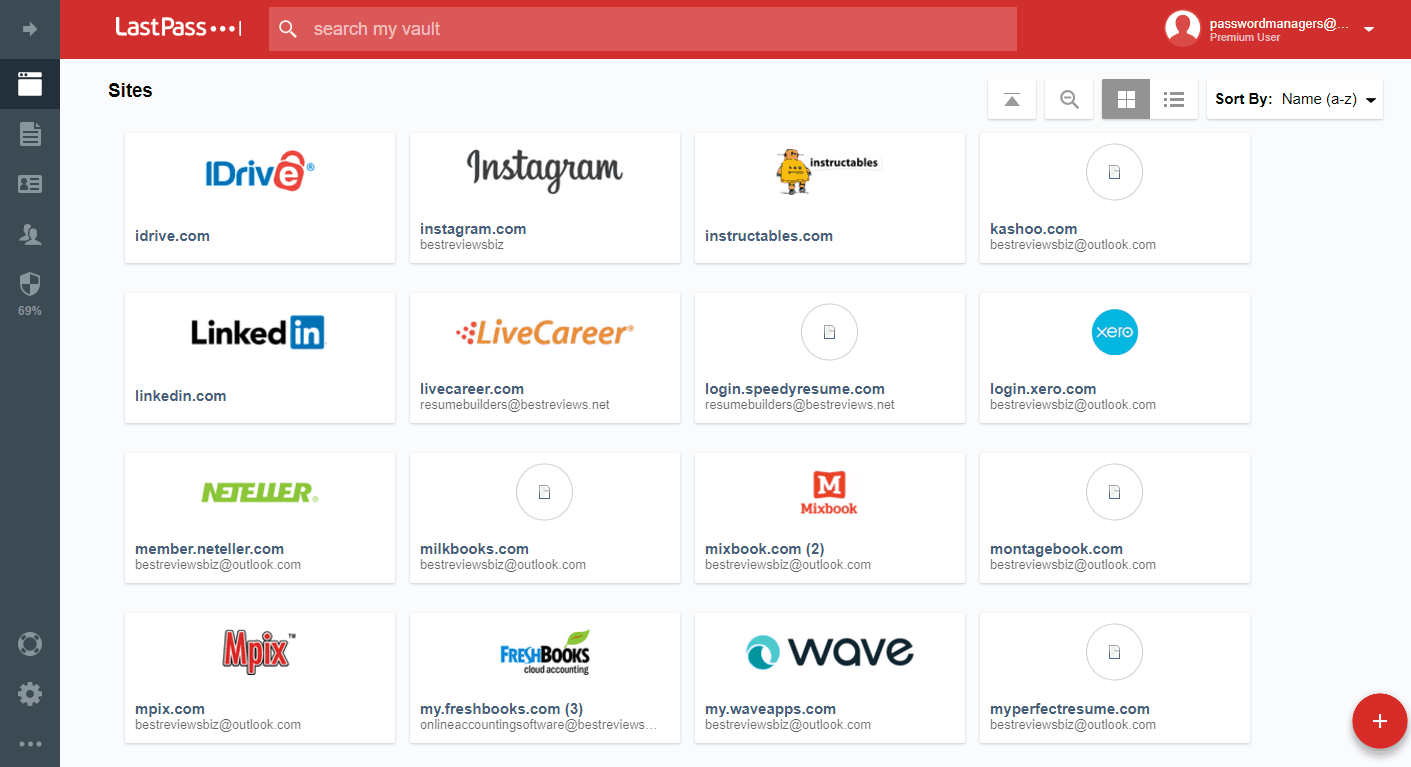
Vault
The vault is the virtual storage of the password manager where all of your passwords and other credentials can be found. The vault can be accessed either from the password manager itself or by visiting a dedicated site provided by the program’s developer. No matter how you access your vault, it is protected by your master password – even accompanied by two-factor authentication – plus all stored data is duly encrypted by the software. Vaults also feature the option of sharing certain credentials with those people you add to the trusted parties list, but usually there is an option to share certain passwords with others in cases of emergency too.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
Get the Best Deals on Password Managers
Subscribe to our monthly newsletter to get the best deals, free trials and discounts on password managers.