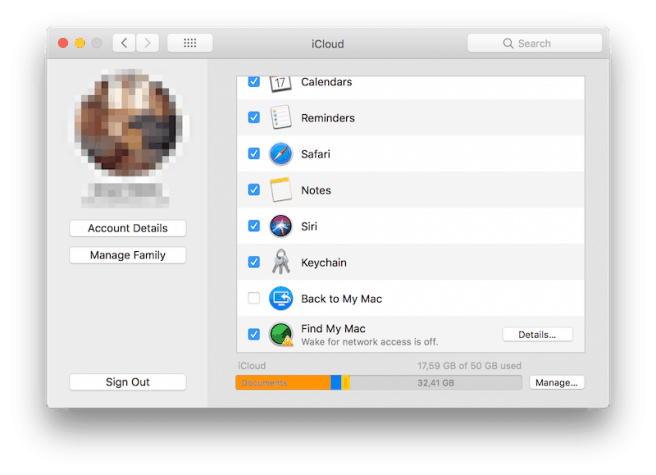
Over the last few years Apple has been expanding its iCloud service to include a convenient feature called iCloud Keychain, which stores the Safari user's account name and passwords, credit card information and Wi-Fi network passwords across all trusted devices running iOS 7.0.3 or later or macOS 10.9 Mavericks or later. It ensures Mail accounts, contacts, calendar details, and messages are all up-to-date across all devices.
Over the last few years Apple has been expanding its iCloud service to include a convenient feature called iCloud Keychain, which stores the Safari user's account name and passwords, credit card information and Wi-Fi network passwords across all trusted devices running iOS 7.0.3 or later or macOS 10.9 Mavericks or later. It ensures Mail accounts, contacts, calendar details, and messages are all up-to-date across all devices.
However, as the number of cyber attacks grows day by day, Apple users are obviously questioning the security of iCloud Keychain, especially in the light of recent reports that iCloud had been hacked.
Just as with password managers, it’s important to understand the security measures Apple has taken to protect your data. Let’s take a look at a short technical background of the service and its overall security.
iCloud Keychain Security
Due to Apple's commitment to privacy and security, the data stored in iCloud Keychain remains protected even if the user's iCloud account has been compromised. This is true even if iCloud is compromised by an external attack or a third party accesses user accounts.
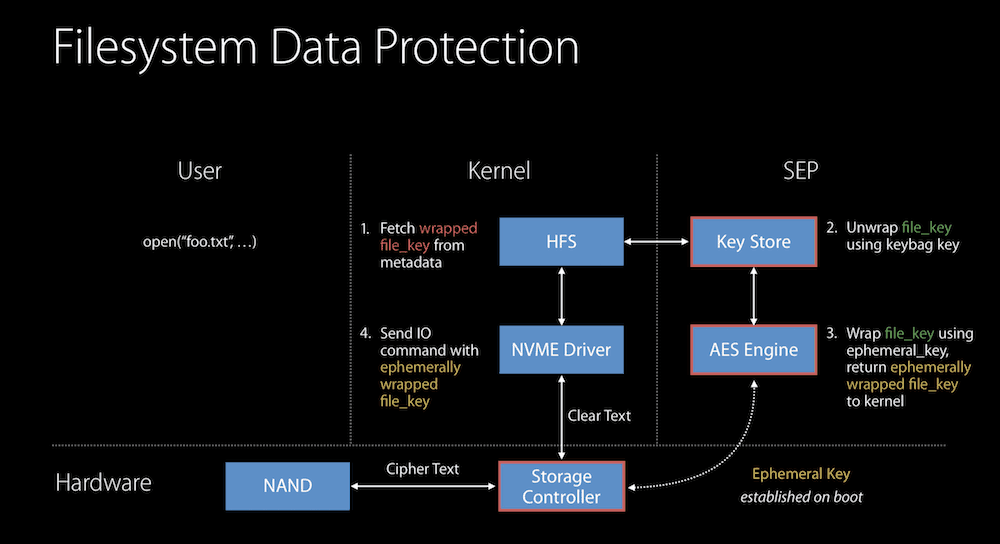
Not even Apple can read your data, which is something that the company has openly claimed in its annual iOS Security whitepaper. iCloud Keychain uses a 256-bit AES encryption to store and transmit passwords and credit card information. It also uses elliptic curve asymmetric cryptography and key wrapping, explained below.
When a user enables iCloud Keychain for the first time, the device establishes a circle of trust and creates a syncing identity for itself. The syncing identity contains the public key that must be signed twice by two additional keys to be validated: the private key (the asymmetric half of the syncing identity), and an asymmetric elliptical key that is derived from your Apple ID password. The circle of trust also contains the parameters used to create the key based on the Apple ID password. This syncing circle is then placed in the cloud where all authorized devices are able to reach it.
When you set up iCloud Keychain on a new device, the previous device that originally created the circle of trust and syncing identity will receive a notification requesting approval for this new access. If you have two-factor authentication enabled, you will be able to activate iCloud Keychain without authorization from the original device.
As soon as the additional device is approved, iCloud Keychain automatically begins updating on that device. Here is what happens from a technical standpoint: the new device notices the syncing circle in iCloud, and that it isn't yet connected to it. To participate within this circle, the new device then creates a syncing identity key pair, followed by an application ticket to the circle.
This ticket will contain the public key for its syncing identity and is signed by a key that is generated from the Apple ID password, at which point the user verifies and approves the ticket on the initial device. As a result, the first device adds the public key of the new member to the syncing circle of trust and places it in iCloud. Finally, both members of the circle sign in and start exchanging data, with priority given to the device that was modified later.
iCloud Keychain vs Password Manager
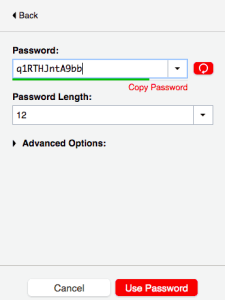 When comparing 1Password, LastPass, or Sticky Password with iCloud keychain we can say that, in terms of security – since both Apple and password management developers have applied a variety of layers of security to protect your data – it would be hard to choose a winner.
When comparing 1Password, LastPass, or Sticky Password with iCloud keychain we can say that, in terms of security – since both Apple and password management developers have applied a variety of layers of security to protect your data – it would be hard to choose a winner.
But there is another aspect that’s important to consider: ease of use. That's where password managers step into the picture, since they deliver cross-platform services and protect your data by encrypting it. If you are only using Apple's services and therefore only need to memorize passwords for these accounts, then iCloud Keychain will be more than enough for you. But if you are using multiple browsers and operating systems, then having all your passwords to hand is possible only with a password manager.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
More iCloud Keychain FAQs
- How Do I Access iCloud Keychain on Windows?
- How Do I See My Passwords in iCloud Keychain?
- How Do I Set Up iCloud Keychain on an iPhone?
- Is Apple’s iCloud Keychain Safe to Use?
- Should I Use iCloud Keychain?
Get the Best Deals on Password Managers
Subscribe to our monthly newsletter to get the best deals, free trials and discounts on password managers.