Web browsers have a problematic feature that, rather unfortunately, we all love to use: autofill. Whenever you create an account on a website, the browser's in-built password manager feature called autofill offers to save the credentials (or any credit card data if applicable) so that next time you visit the site it will automatically fill in the required fields, requiring you just press the enter key to log in.
But the price of this convenience is high risk to security. Research released through Princeton's Center for Information Technology Policy reveals how browsers' built-in password managers fail to protect user data and in fact give it away to online advertising and data tracking firms.
At the heart of the problem is the convenient autofill feature. While it streamlines the login process, it falls prey to third-party scripts that harvest email addresses and, if used for malicious purposes, will also leak passwords.
A Security Flaw No One Talks About
The fact is that this isn't a new security flaw. The security community has been aware of it for the past decade and it hasn’t stopped being a topic of discussion since, but this research is the first to publicly disclose the root cause of this security vulnerability that allows hackers to easily harvest your credentials.
Actually, David Silver, Suman Jana, and Dan Boneh from Stanford University, as well as Eric Chen and Collin Jackson from the Carnegie Mellon University, each conducted a number of theoretical attacks on the leading browsers' built-in password managers and password management services' autofill features. What they discovered was quite alarming: these services follow very different and inconsistent autofill policies.
The researchers demonstrated how a malicious attack can be successful in an ‘evil coffee shop’ because of the autofill policy. They also demonstrated how password managers can prevent these malicious attacks by never autofilling in certain conditions and requiring manual user interaction before the software automatically enters any password.
Why Is This Still Possible?
 All popular browsers have their own built-in password managers that save and fill usernames and passwords to streamline the login process. In general, the login form doesn't require any user interaction, with some of the major web browsers filling in the credentials automatically regardless of how visible to the user that form is.
All popular browsers have their own built-in password managers that save and fill usernames and passwords to streamline the login process. In general, the login form doesn't require any user interaction, with some of the major web browsers filling in the credentials automatically regardless of how visible to the user that form is.
As a result, third-party scripts can easily abuse this browser feature to retrieve the saved credentials simply by creating a form with the username and password field, hide it on the legitimate page, and the browser autofill will do the rest by automatically entering the stored data into the required fields.
This isn't a new flaw and unfortunately it will stick around for some while, because from the browser's perspective there is no flaw. Everything is working as it was designed to do. Here is why.
The web application security model relies on something called Same-Origin Policy. Under this rule, the web browser allows scripts contained in an initial web page to access data in a second web page if they have the same origin, aka domain or website. So, if a web-based service provider embeds a third-party script on its site instead of isolating it in an iframe (an inline frame is used to embed another document within the current HTML document), then the web browser will treat the script as though it is coming from the publisher (web service provider). As a result, nothing can stand in the way of a hacker extracting the credentials automatically filled in by the browser's password manager.
What Can You Do to Protect Yourself?
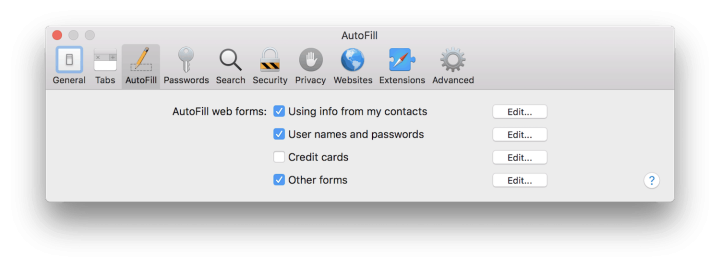
The easiest way to protect yourself is to disable autofill in any browser you use. Actually, if you use a password management service – which we highly recommend – then they will instruct you on how to disable the browser autofill. It's important to complete this step, because password management services will help you to address this serious security flaw by first verifying the authenticity of the website that you are trying to log in to, and then require your input to fill in the credentials before safely logging in.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
Get the Best Deals on Password Managers
Subscribe to our monthly newsletter to get the best deals, free trials and discounts on password managers.


Share Your Comment