 Just as the tech industry is turning its attention from passwords to biometric identification, so are hackers. It may come as a surprise – or maybe not – that with the abundance of photos we share about ourselves on various platforms, hackers don't need some sci-fi technology to hack our body or steal our physical characteristics in order to fool biometric identification systems. They can do it without even having physical contact with us.
Just as the tech industry is turning its attention from passwords to biometric identification, so are hackers. It may come as a surprise – or maybe not – that with the abundance of photos we share about ourselves on various platforms, hackers don't need some sci-fi technology to hack our body or steal our physical characteristics in order to fool biometric identification systems. They can do it without even having physical contact with us.
Hacking Touch ID
Take Touch ID, for example, which was introduced by Apple with the iPhone 5s. To those who may be unaware, Touch ID is a fingerprint recognition system that has been added to iPhones, iPads, and more recently to MacBook Pros with Touch Bar. The white-hat hackers of Germany-based Chaos Computer Club were able to find a workaround shortly after the device hit the shelves.
![]() What raises a red flag is that they were able to hack Touch ID simply by photographing the fingerprint of the phone owner. The aim of the experiment was to demonstrate that fingerprint biometrics are not suitable for controlling access to personal devices and should be avoided.
What raises a red flag is that they were able to hack Touch ID simply by photographing the fingerprint of the phone owner. The aim of the experiment was to demonstrate that fingerprint biometrics are not suitable for controlling access to personal devices and should be avoided.
Hacking an Iris Scanner
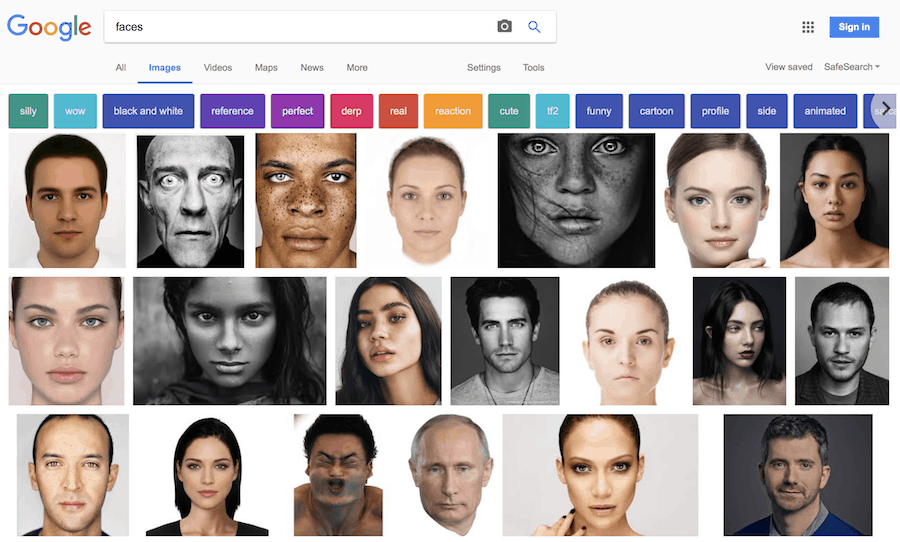
 While photographing a fingerprint may require some skills not all hackers have access to, a new biometric solution, iris scanning, has made things easier for them. Especially when considering that social media platforms are flooded with high-resolution images showing users’ faces.
While photographing a fingerprint may require some skills not all hackers have access to, a new biometric solution, iris scanning, has made things easier for them. Especially when considering that social media platforms are flooded with high-resolution images showing users’ faces.
In another experiment initiated by the same CCC, security researcher Jan “Starbug” Krissler has found that an attack can be carried out against some iris-scanning kits by simply making use of images found in Google searches. The only condition pictures need to meet is that they are vivid and a high enough resolution. That means it’s possible for hackers to simply print copies of the target's eyes and bypass biometric authentication.
Starbug first showed off a clone of the thumbprint of Ursula von der Leyen, Germany's defense minister. That was in December 2014, but a few years later he showed that it was possible to do the same with eyes simply by doing a Google search. If the image was clear, vivid and in high-resolution, bypassing the biometric authentication was possible.
That's how he was able to print out high-resolution pics of the eyes of high-profile politicians such as Vladimir Putin, David Cameron and Hilary Clinton. He wasn't able to use these printouts, though, because he didn't have access to the devices these people were using.
What raises concern is that while fingerprint hacking required a proper clone, which took time, the iris scan hack required only a high-resolution print. Considering that some high-tier Android handsets feature an iris scanner – such as the Samsung Galaxy S8 launched in early 2017 – unlocking that device using biometrics would be as easy as showing a picture, as demonstrated by the CCC. But the video demonstrates that the iris-scanning technology used in this particular device is far from providing a high-level of security.
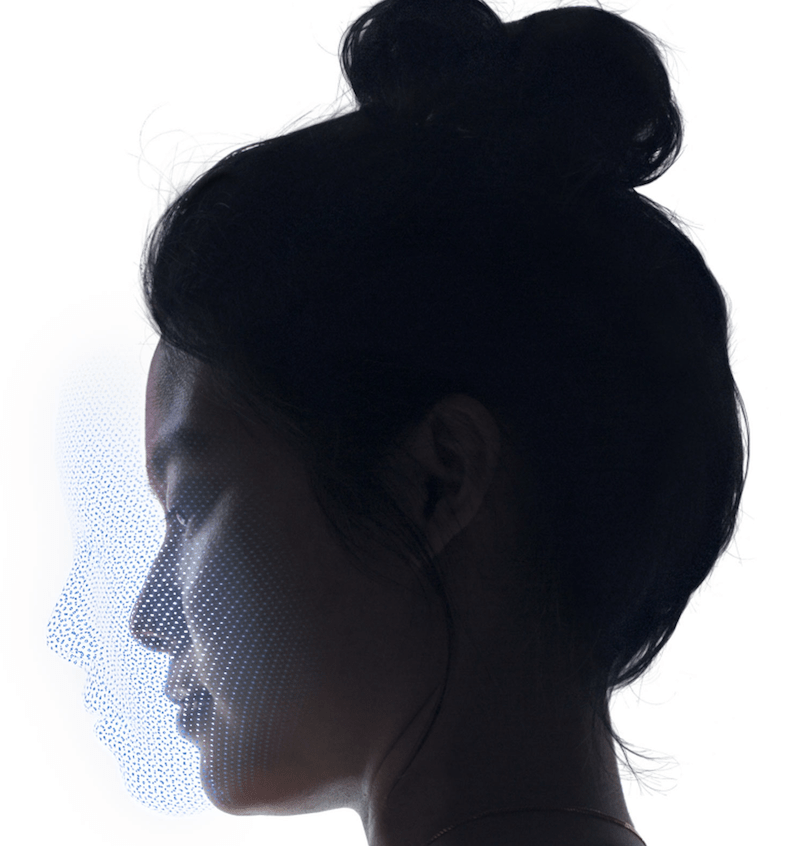
Face ID
Apple has introduced Face ID with the iPhone X – claiming facial recognition is more secure than fingerprint identification – and has tilted interest in the industry towards this direction. The biometric authentication uses a TrueDepth camera system with advanced technologies to accurately map the geometry of the user's face, projecting and analyzing more than 30,000 invisible dots to create a 3D map of the face.
As of writing this article the iPhone X has yet to be released, so we can't comment on the actual level of security of this system. What we know, however, as users of biometric authentication, is that it will bring convenience to our digital lives.
Why Biometrics Can’t Replace Passwords
 Still, there is an issue that all users need to be reminded of, and Starbug's experiments highlight once again that you can't hide your body's physical characteristics: your face, your eyes, your fingerprints. Passwords, on the other hand, can be hidden and encrypted. Relying on biometrics as the only authentication method is like being off-guard all the time. Enable two-factor authentication and use strong passwords combined with a good password manager to ensure you have access to all your passwords in an instant.
Still, there is an issue that all users need to be reminded of, and Starbug's experiments highlight once again that you can't hide your body's physical characteristics: your face, your eyes, your fingerprints. Passwords, on the other hand, can be hidden and encrypted. Relying on biometrics as the only authentication method is like being off-guard all the time. Enable two-factor authentication and use strong passwords combined with a good password manager to ensure you have access to all your passwords in an instant.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
Get the Best Deals on Password Managers
Subscribe to our monthly newsletter to get the best deals, free trials and discounts on password managers.

Share Your Comment