 Everybody knows that strong passwords are the only way to make sure our online data stays safe and, thankfully, many users have finally understood the importance of properly securing their online privacy. But still, there’s a long way to go until everyone can surf the internet without fear of having their most sensitive data compromised.
Everybody knows that strong passwords are the only way to make sure our online data stays safe and, thankfully, many users have finally understood the importance of properly securing their online privacy. But still, there’s a long way to go until everyone can surf the internet without fear of having their most sensitive data compromised.
However, preventing yourself from becoming the latest victim of data theft is not as complicated as it may seem; as a matter of fact, by following these five easy steps hackers will definitely keep clear of your accounts.
Step 1: Use the Heavy Artillery, Password Managers
If you haven’t done so already, it’s highly recommended to subscribe to the services of a password management solution, one of the best ways to make online accounts completely hacker-proof.
In fact, there are a few reasons why a password manager is considered to be the ultimate protector of the online privacy for internet users:
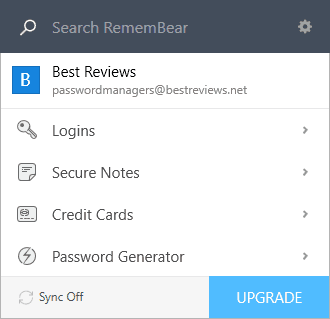
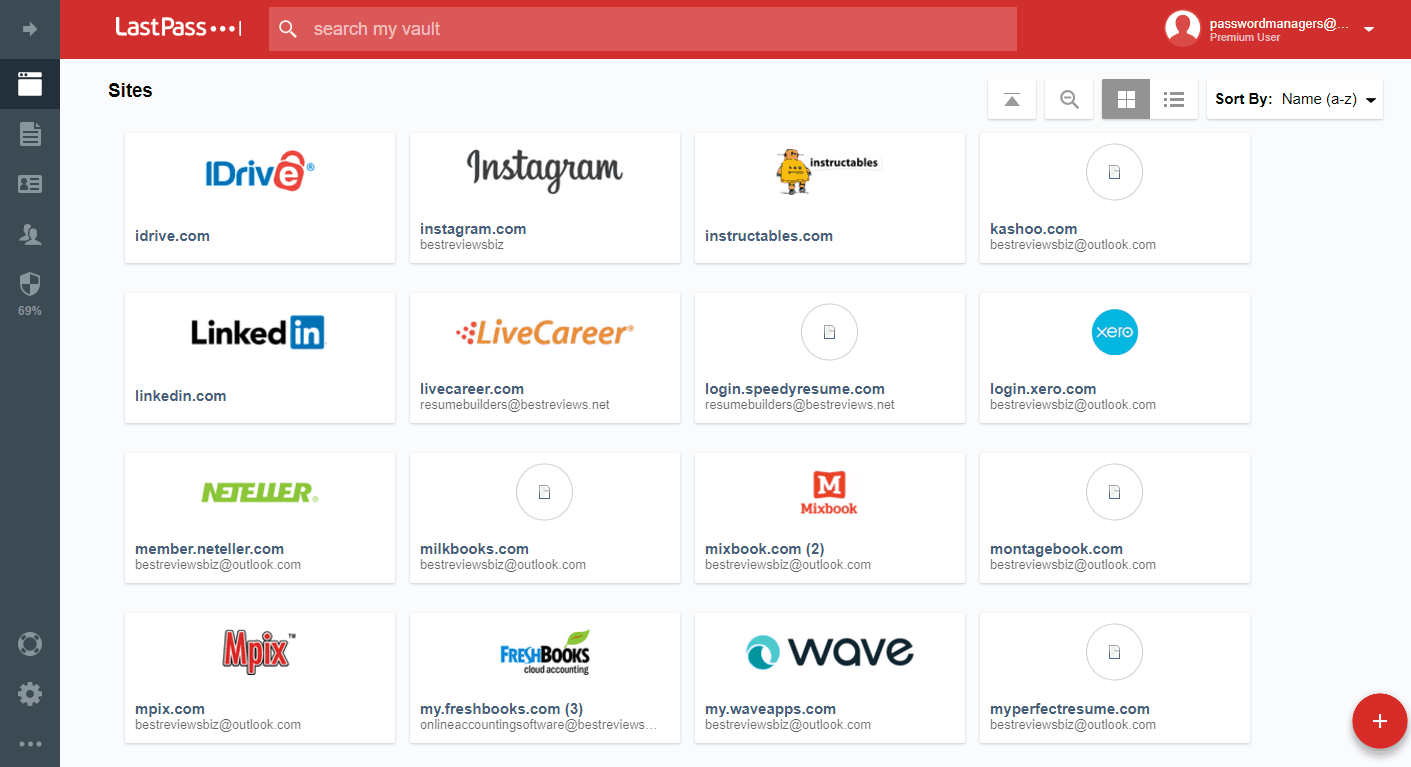
- Password managers come with military-grade encryption by default, which means that nobody, not even the software’s developer, is able to see what kind of information – whether that be passwords, credit card data, licenses, secure notes and the like – is stored in the password manager’s vault.
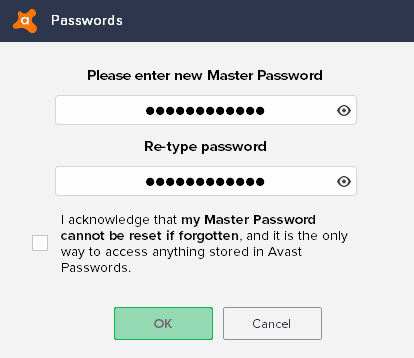
- Password managers can only be accessed with the so-called master password that can be further complemented with additional authentication options, such as biometric authenticators, two-factor authentication apps (see below) or special security tokens.
- Most password management software comes with browser add-ons that are capable of not only fetching all the passwords and credentials that are stored in the browser’s own password manager, but also conveniently autofilling forms and login screens with that saved data.
- Thanks to this autofilling it is easy to simply replace old passwords with new, stronger ones and store them in the program’s safe vault without the need to remember them. As a matter of fact, the use of a password manager reduces the number of passwords to be memorized to just one: the aforementioned master password.
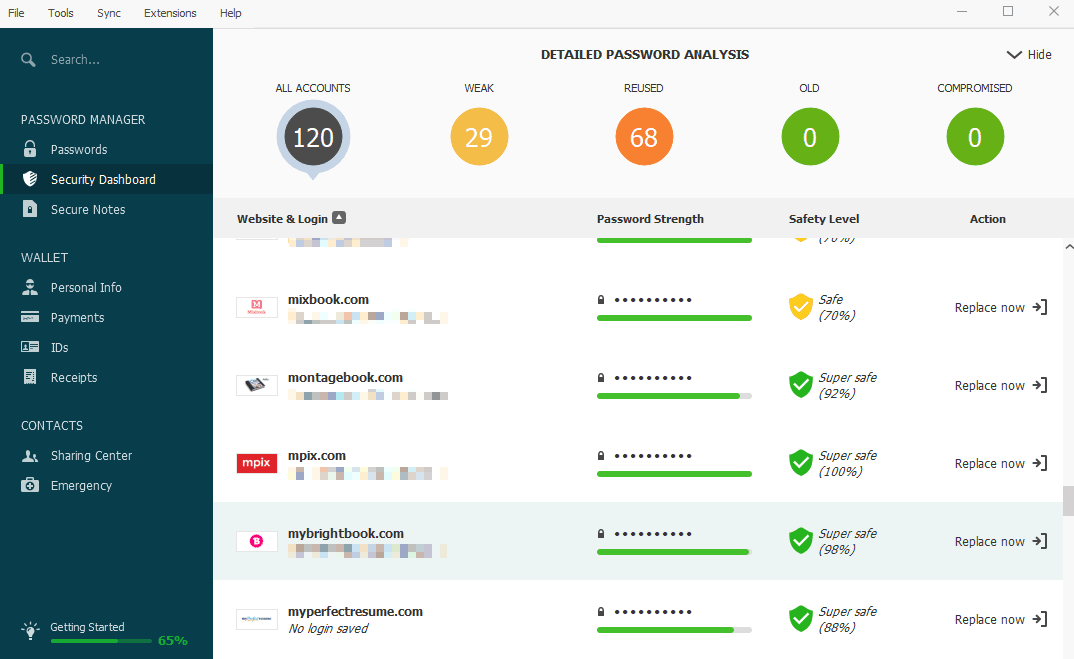
- Password managers often provide various extra features, too, such as seamless data syncing between devices, the secure sharing of passwords, automated login, a detailed analysis of passwords stored in the vault, and the list could go on.
Step 2: The Longer the Password the Better
Granted, it’s quite hard to come up with a complex password. But if you want to protect yourself well then it’s practically mandatory, since the more characters the password contains the more difficult it will be for hackers to crack it.
There are various ways to come up with a long and strong password: one such option is to generate one with an online password generator or the built-in tool of password managers. Another option to consider is to think of a word or expression that you can easily remember and then change upper case letters to lower case ones – and vice versa – and/or replace certain letters with non-standard characters or numbers that resemble the original letter.
Step 3: Mixing up Those Special Characters
Speaking of those non-standard characters, there is a small rule regarding those: if the password is filled with special characters, then it’s best to separate them from one another. In simpler words, a non-standard character shouldn’t be immediately followed by another but, instead, one or more letters or numbers.
Step 4: Don’t Trust Browsers With Managing Your Passwords
As tempting as it may be to trust our web browsers with our most sensitive data, it is like serving our credentials up on a silver plate. For starters, the built-in password vaults of browsers are not hacker-proof at all. And if that’s not problematic enough, if the browser doesn’t have proper privacy settings your data could be compromised even easier – and not just by wrongdoers, but even the browser’s developer or third party services, too.
Step 5: Reinforcing Security With Two-Factor Authentication
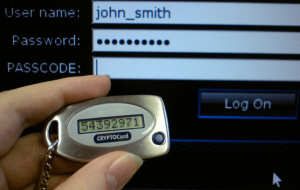 Although it is often confused with two-step verification, two-factor authentication – or 2FA for short – is actually safer because the second step in the authentication process happens on a separate device like a hardware token or a trusted device that generates the temporary code. This way even if the password to the account does get stolen by hackers, they can’t break into the targeted account as they are not in possession of the necessary secondary key to complete the login process.
Although it is often confused with two-step verification, two-factor authentication – or 2FA for short – is actually safer because the second step in the authentication process happens on a separate device like a hardware token or a trusted device that generates the temporary code. This way even if the password to the account does get stolen by hackers, they can’t break into the targeted account as they are not in possession of the necessary secondary key to complete the login process.
Although security keys are considered to be the best solution for 2FA, apps like Google Authenticator or Authy can also be trusted, not to mention they can be paired with various services – even password managers.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
Get the Best Deals on Password Managers
Subscribe to our monthly newsletter to get the best deals, free trials and discounts on password managers.

Share Your Comment