 Since web services that care about security have moved toward two-factor authentication (2FA), some of us – such as Wall Street Journal writer Christopher Mims – have become confident enough not to use secure passwords because the second layer of security means it’s tougher to hack an account. But it’s the second part in the 2FA security process that can become the weak link that could open the door to your online accounts and allow hackers to lock you out of your digital life.
Since web services that care about security have moved toward two-factor authentication (2FA), some of us – such as Wall Street Journal writer Christopher Mims – have become confident enough not to use secure passwords because the second layer of security means it’s tougher to hack an account. But it’s the second part in the 2FA security process that can become the weak link that could open the door to your online accounts and allow hackers to lock you out of your digital life.
The Weak Link in Your Security
Enabling two-factor authentication or two-step verification may feel like a security blanket because it gives the impression that your online data is protected by an invincibility spell. The idea behind this extra level of security is to test someone's identity based on something they know (that's your password) and something that person should have access to (that's the mobile handset or other device). Apple makes a distinction between two-step verification and two-factor authentication, and recommends upgrading to 2FA because it is a newer security method. For now, any security methods involving two steps in verifying your identity are equally secure.
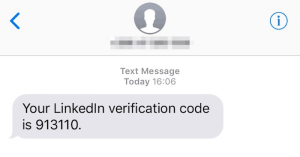
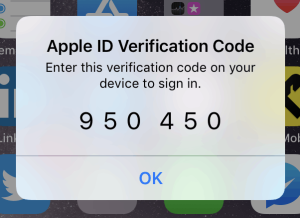 The difference between the two methods is that two-step verification uses verification codes sent via SMS text messages or via Find My iPhone, while 2FA requires a six-digit verification code displayed on trusted devices. As known security researcher and forensics expert Jonathan Zdziarski explains, the problem with text messages sent to your trusted mobile phone number is that “SMS has turned that “something you have” into “something they sent you”.
The difference between the two methods is that two-step verification uses verification codes sent via SMS text messages or via Find My iPhone, while 2FA requires a six-digit verification code displayed on trusted devices. As known security researcher and forensics expert Jonathan Zdziarski explains, the problem with text messages sent to your trusted mobile phone number is that “SMS has turned that “something you have” into “something they sent you”.
Real-life usage has demonstrated that SMS-based two-factor authentication is often the weakest link in two-step identity verification: just think about the attacks on political activists in Iran and Russia or, to cite a more recent example, TechCrunch's writer John Biggs. All of them were hacked and found themselves locked out of their digital lives after hackers impersonated their accounts and, in Bigg's case, attempted to collect money in Bitcoin from his friends.
How Was That Possible?
 There are various methods hackers can use, and one of them is to call your mobile network carrier and swap their SIM card with yours. In fact, the number of SIM swaps was so high in New York that it has prompted the New York State Department of State's Division of Consumer Protection to alert AT&T customers about the scheme that allows scammers to switch the target's SIM card to a new device. From that moment on, they were able to intercept all SMS messages – including the verification codes – the user has set up as part of the two-step verification process.
There are various methods hackers can use, and one of them is to call your mobile network carrier and swap their SIM card with yours. In fact, the number of SIM swaps was so high in New York that it has prompted the New York State Department of State's Division of Consumer Protection to alert AT&T customers about the scheme that allows scammers to switch the target's SIM card to a new device. From that moment on, they were able to intercept all SMS messages – including the verification codes – the user has set up as part of the two-step verification process.
Another method is the use of fake cell phone towers known as IMSI catchers or “stingrays”. These devices can intercept text messages and calls.
Additionally the security community has been warning carriers about the existence of weaknesses in the Signaling System 7 (SS7) protocol that allows telecom networks to communicate with each other. This security flaw can be used to intercept two-factor authentication codes, which once again leaves you vulnerable to hacker attacks. If that temporary code sent as a text message is set up to help you log in to your online banking platform, you may end up with an empty account.
That's a nightmare you don't want to experience, we can all agree on that. If you have so far managed to fly under the radar of hackers, there could still become a time when you will also be hacked if you're not prepared.
What Can You Do?
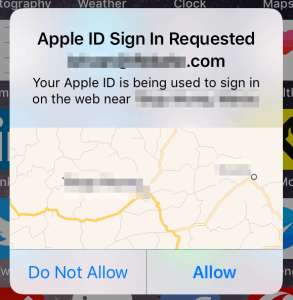 First, you can upgrade the security level of two-factor authentication services to push notifications sent to trusted devices instead of SMS messages. If you need to stick with SMS, you can set up a security PIN or passcode to your phone's wireless account. That PIN should be different from the PIN used to unlock the smartphone.
First, you can upgrade the security level of two-factor authentication services to push notifications sent to trusted devices instead of SMS messages. If you need to stick with SMS, you can set up a security PIN or passcode to your phone's wireless account. That PIN should be different from the PIN used to unlock the smartphone.
Storing your PIN and/or strong passwords can be done with a secure notebook, but using a password manager would do just as well. That way, you need to remember only your master password and let the service do the rest: store backup codes, PIN codes, passcodes, and much more. And if you are using a good password manager, you can even set it up to work with services working with one-time passcodes generated by services such as the Google Authenticator app or Authy.
Best Password Managers of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024
|
|
|
2
|
 |
|
|
|
3
|
|
Get the Best Deals on Password Managers
Subscribe to our monthly newsletter to get the best deals, free trials and discounts on password managers.

Share Your Comment