 Everybody has their own method for storing credentials: some rely on sticky notes, others use spreadsheets, while there are many who think that password managers are the only solution. Either way, we all strive for the same goal: to keep our most sensitive data safe at any cost. However, there is a particular way of storing passwords that not too many people think of: a password logbook. Read More…
Everybody has their own method for storing credentials: some rely on sticky notes, others use spreadsheets, while there are many who think that password managers are the only solution. Either way, we all strive for the same goal: to keep our most sensitive data safe at any cost. However, there is a particular way of storing passwords that not too many people think of: a password logbook. Read More…
Password Managers Articles
FIDO: A Trustworthy Companion for Faster Authentication
 Whether we like it or not, passwords are something we have to live with in order to be able to access various online services. But the fact that people are still using passwords that are incredibly easy to crack – despite the continuous warnings of security experts – proves that sooner or later developers must come up with a solution that is not only secure but is also able to either complement or fully replace those pesky passwords.
Whether we like it or not, passwords are something we have to live with in order to be able to access various online services. But the fact that people are still using passwords that are incredibly easy to crack – despite the continuous warnings of security experts – proves that sooner or later developers must come up with a solution that is not only secure but is also able to either complement or fully replace those pesky passwords.
Laptops and smart devices are already capable of replacing passwords and passcodes or serve as one of the steps in the two-factor authentication process, but it is the latter that is the very thing that FIDO, the next step in secure online authentication, is built on. Read More…
Spreadsheet Templates for Storing Passwords: The Good Old Approach
 In an age when passwords are required to be complex in order to be unbreakable by hackers, having credentials stored in a place where they can be accessed easily is a must. Most people still trust sticky notes, while others simply put their login information into different files without paying attention to proper organization. As you might expect, the result of this is nothing short of pure chaos.
In an age when passwords are required to be complex in order to be unbreakable by hackers, having credentials stored in a place where they can be accessed easily is a must. Most people still trust sticky notes, while others simply put their login information into different files without paying attention to proper organization. As you might expect, the result of this is nothing short of pure chaos.
That’s why many people decide to create a password spreadsheet or, better yet, download a password template from the internet, and organizing passwords all of a sudden becomes easier and smarter. Read More…
Can Your Heart Beat the Password?
Since 1964 cardiologists have known that everyone's heartbeat is unique and influenced by different factors such as the heart's size, shape and position in the body. So since it is so unique, can your heartbeat be used as a password? Scientists certainly think it is possible. Read More…
How to Change Your Security Camera’s Password
 We’re not trying to creep you out, but someone may be watching you back home, on the street, or in your office… you name it, wherever you are there may be eyes on you. This isn't a scene from a science-fiction movie, either, it's what the current technology of web-connected cameras enable hackers to do. Read More…
We’re not trying to creep you out, but someone may be watching you back home, on the street, or in your office… you name it, wherever you are there may be eyes on you. This isn't a scene from a science-fiction movie, either, it's what the current technology of web-connected cameras enable hackers to do. Read More…
The Best Open Source Password Managers of 2020
 When it comes to keeping passwords and other credentials in a convenient cloud vault without worrying about attacks from hackers, there is no compromise; this means choosing a password manager that is user-friendly and includes every feature that could keep even the most sensitive data safe. This is why most people have doubts when they hear the terms “open source” and “password manager” put together.
When it comes to keeping passwords and other credentials in a convenient cloud vault without worrying about attacks from hackers, there is no compromise; this means choosing a password manager that is user-friendly and includes every feature that could keep even the most sensitive data safe. This is why most people have doubts when they hear the terms “open source” and “password manager” put together.
While the fact that open source programs are free of charge is worthy of praise, when average users hear that the software’s source code can be accessed publicly they might immediately and unfairly assume that this also means greater vulnerability.
However, most open source password managers are on par with or, sometimes, even better than their commercial counterparts – and we have six examples to prove that. Read More…
How to Make a Strong Password You Can Remember
 Have you discovered the secret of creating secure passwords and yet being able to easily recall them at will without any outside help? Considering the frequency of data breaches these days, this is something that all internet users need to address in some way, whether that’s by developing a set of rules that ease both password generation and recalling them at will or by using a password manager.
Have you discovered the secret of creating secure passwords and yet being able to easily recall them at will without any outside help? Considering the frequency of data breaches these days, this is something that all internet users need to address in some way, whether that’s by developing a set of rules that ease both password generation and recalling them at will or by using a password manager.
If you have set up your own personal system to manage unique, randomized and unbreakable passwords, you can count yourself among a rare group of people who don't use the same passwords over and over again. Read More…
Stop Using SMS as Second Factor in the Authentication Process
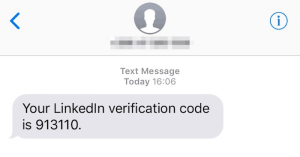 Since web services that care about security have moved toward two-factor authentication (2FA), some of us – such as Wall Street Journal writer Christopher Mims – have become confident enough not to use secure passwords because the second layer of security means it’s tougher to hack an account. But it’s the second part in the 2FA security process that can become the weak link that could open the door to your online accounts and allow hackers to lock you out of your digital life. Read More…
Since web services that care about security have moved toward two-factor authentication (2FA), some of us – such as Wall Street Journal writer Christopher Mims – have become confident enough not to use secure passwords because the second layer of security means it’s tougher to hack an account. But it’s the second part in the 2FA security process that can become the weak link that could open the door to your online accounts and allow hackers to lock you out of your digital life. Read More…
How Secure Is Two-Factor Authentication?
You may not be aware of it, but you were using two-factor authentication (2FA) before it became widespread in protecting online accounts. Just think about the moment you withdraw cash from an ATM: you have the physical card, but you still need to know the PIN.
In fact, 2FA is recommended to anyone protecting highly sensitive data, but apparently, even some of the biggest companies don't implement it, which leaves them vulnerable to hacker attacks. The use of 2FA would have prevented high profile data breaches such as that of Deloitte, one of the big four accountancy companies worldwide, for example. Read More…
3 Reasons Biometrics Won’t Replace Passwords Anytime Soon
 Former Microsoft chairman Bill Gates predicted the death of the traditional password in 2004, saying it “cannot meet the challenge” of keeping sensitive information secure. According to his forecast, users across the globe are going to use passwords less and less, at which point he then demonstrated ‘tamper resistant’ biometric ID card software that allows companies to identify their employees using biometric technology. Read More…
Former Microsoft chairman Bill Gates predicted the death of the traditional password in 2004, saying it “cannot meet the challenge” of keeping sensitive information secure. According to his forecast, users across the globe are going to use passwords less and less, at which point he then demonstrated ‘tamper resistant’ biometric ID card software that allows companies to identify their employees using biometric technology. Read More…
- « Previous Page
- 1
- …
- 10
- 11
- 12
- 13
- 14
- …
- 16
- Next Page »

