Many users don't realize it, but that tiny, always-on device gathering dust in the corner can become a spy in your house. Don't look any further than your router, though, because that's the device that is eyed by many cybercriminals and even intelligence agencies, as documents released by Edward Snowden show. Read More…
Password Managers Articles
5 Tips for Safer Online Shopping
 You have every reason to prefer shopping online rather than in a brick-and-mortar store, since you get both the bargains and the convenience of shopping in the comfort of your home. On top of that, the products are delivered directly to your doorstep, so all you need to do is open that frustration-free package to enjoy the purchase. Read More…
You have every reason to prefer shopping online rather than in a brick-and-mortar store, since you get both the bargains and the convenience of shopping in the comfort of your home. On top of that, the products are delivered directly to your doorstep, so all you need to do is open that frustration-free package to enjoy the purchase. Read More…
Convenience vs Internet Security: Which Side Are You On?
The majority of American adults have fallen victim to some type of data theft or fraud at least once, but despite their experiences and voiced concerns many do not follow digital security best practices in their personal lives. Instead, the trend is to prefer access at anytime, anywhere, and not just from PCs and laptops but also from mobile devices. Users want the same convenience and flexibility that they enjoy on smart devices. Read More…
How to Maximize Your Email Account Security
You probably haven't thought about it, but what's the first thing you do after killing the alarm in the morning? Most people will either check their social media accounts or launch the mail client – the order is not important in this case.
Email has become central to our digital life: it's what we use to create a social media profile, it's how we get in touch with people, and it's the place where we store our contacts for friends, family, and work. Your email inbox also includes newsletters, subscriptions, documents, pictures, and so much more. You might not realize it but our digital presence is built around email, essentially making it the home of our digital life. Read More…
The Majority of Gmail Users Still Don’t Use 2FA
 Two-factor authentication has been available for more than seven years but still no one is using it to protect their account. Google introduced its two-step authentication for Gmail accounts and gave users the option to strengthen their account security, but didn't make it mandatory. Fast-forward to today, where less than 10% of active Google accounts use two-step verification (2SV). Read More…
Two-factor authentication has been available for more than seven years but still no one is using it to protect their account. Google introduced its two-step authentication for Gmail accounts and gave users the option to strengthen their account security, but didn't make it mandatory. Fast-forward to today, where less than 10% of active Google accounts use two-step verification (2SV). Read More…
Facebook Wants to Become the Password Manager of Your Digital Life
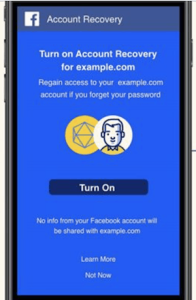 Forget email and recovery questions, because next-generation account recovery will be through Facebook. At least this is how the social media giant hopes to lock the next billion users into its platform. It looks as though scrolling through endless newsfeeds is no longer enough, as Facebook is close to living up to its name and will give a face to the billions of people connected to the internet. It would like to become the platform through which users will recover the password to any third-party account via its new service called Delegated Account Recovery. Read More…
Forget email and recovery questions, because next-generation account recovery will be through Facebook. At least this is how the social media giant hopes to lock the next billion users into its platform. It looks as though scrolling through endless newsfeeds is no longer enough, as Facebook is close to living up to its name and will give a face to the billions of people connected to the internet. It would like to become the platform through which users will recover the password to any third-party account via its new service called Delegated Account Recovery. Read More…
Should You Share Passwords With Your Girlfriend or Boyfriend?
Once their toothbrush is in the bathroom, it becomes a question of when – not if – your partner or spouse will ask the magic question: ‘Hey, what's your password to your account? I need to check something.’ Read More…
When Passwords and Security Questions Fail
The average person thinks about password security only when they get a notification saying that one of their accounts was compromised or when they forget the current password and need a new one. Passwords and security questions form the first line of defense and have the role of protecting an account from intruders. Read More…
Password Strength Meters Aren’t as Useful as You Might Think
Passwords are the first line of defense for safeguarding data stored in online accounts, although there have been many proposals for replacements: just consider the presence of biometrics on smartphones. Now, every high-end smartphone includes some sort of biometric identification feature, whether that’s an iris or fingerprint scanner or the new facial recognition system called Face ID by Apple. Read More…
Why You Should Never Use Unlock Patterns
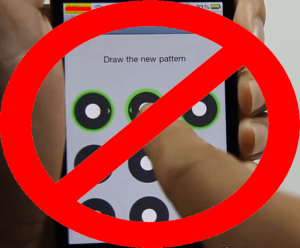 Thanks to the advancement of technology, there are various methods for securing our devices. Turning on any of these advanced protection methods – whether that be facial and voice recognition, fingerprint scanning or passwords – ensures that even if the device falls into the wrong hands there is no way that the hacker can get access to your most precious data.
Thanks to the advancement of technology, there are various methods for securing our devices. Turning on any of these advanced protection methods – whether that be facial and voice recognition, fingerprint scanning or passwords – ensures that even if the device falls into the wrong hands there is no way that the hacker can get access to your most precious data.
However, not everyone can enjoy the benefits of modern authentication methods, especially those who are using older smartphone models or prefer less advanced ways of accessing their devices, such as using an unlock pattern on Android phones. But this is something that users should really reconsider since, as it turns out, these graphical passwords are anything but safe. Read More…
- « Previous Page
- 1
- …
- 6
- 7
- 8
- 9
- 10
- …
- 16
- Next Page »