Whether it’s individuals or businesses, everybody knows that in a world where basically everything connects to the internet there is nothing more important than being able to protect personal data. But no matter how many times the importance of cyber security is emphasized and despite the constant pleas of internet security experts, most people still take the protection of sensitive data too lightly. This explains why more and more users fall victim to the various types of cyber attacks each year. Just how problematic is this carelessness of the average user? According to a 2017 study published by Kaspersky, every second business considers its own employees to be the biggest threat to system security. Read More…
Whether it’s individuals or businesses, everybody knows that in a world where basically everything connects to the internet there is nothing more important than being able to protect personal data. But no matter how many times the importance of cyber security is emphasized and despite the constant pleas of internet security experts, most people still take the protection of sensitive data too lightly. This explains why more and more users fall victim to the various types of cyber attacks each year. Just how problematic is this carelessness of the average user? According to a 2017 study published by Kaspersky, every second business considers its own employees to be the biggest threat to system security. Read More…
Password Managers Articles
How to Log in Seamlessly With Passwordless Authentication
 A username or email address and a password: this is the combination that the vast majority of services require users to provide in order to gain access to their accounts. Even if this authentication method is still the most widespread, the average user is frustrated at the thought of coming up with and then memorizing long and complex logins for each account. And this usually leads to either the reuse of the same password over and over – which is insanely reckless – or a desperate search for ways of bypassing the need to remember a set of random characters. However, if passwordless authentication methods – like the one developed by Auth0 – become the industry standard, then we can hopefully say goodbye to those pesky passwords once and for all. Read More…
A username or email address and a password: this is the combination that the vast majority of services require users to provide in order to gain access to their accounts. Even if this authentication method is still the most widespread, the average user is frustrated at the thought of coming up with and then memorizing long and complex logins for each account. And this usually leads to either the reuse of the same password over and over – which is insanely reckless – or a desperate search for ways of bypassing the need to remember a set of random characters. However, if passwordless authentication methods – like the one developed by Auth0 – become the industry standard, then we can hopefully say goodbye to those pesky passwords once and for all. Read More…
How Weak Passwords Contribute to Data Breaches
Another day, another security breach. Data leaks have become part of our everyday lives, made possible by of the abundance of online services we use on a daily basis that all make a good target for hackers. It doesn't even have to be a big corporation either, since it's the small and mid-sized businesses that are commonly the targets of cyber criminals. And if you, as the business owner, don't take the necessary steps to train employees in how to protect business data, then you could be the next target. Read More…
The Cost of Thinking ‘I Have Nothing to Hide’
 How many times have you heard the argument ‘I have nothing to hide, so why should I fear being monitored?' It’s a very attractive idea: you pay your taxes, don't commit crimes, and are loyal to your partner, so indeed, why would you want to hide anything? We are living in a free world, where cyber criminals are hunting only the rich and those who have something to hide.
How many times have you heard the argument ‘I have nothing to hide, so why should I fear being monitored?' It’s a very attractive idea: you pay your taxes, don't commit crimes, and are loyal to your partner, so indeed, why would you want to hide anything? We are living in a free world, where cyber criminals are hunting only the rich and those who have something to hide.
But actually, in a digital era in which there are countless ways to gain access to user data, this false claim gives consumers a sense of overconfidence, which has devastating results both for their bank accounts – $172 billion was stolen from customers in 2017 alone – and personal lives. Read More…
Is It Possible to Hack a Password Manager?
While, yes, it is possible to hack a password manager, don’t jump to the wrong conclusion just yet since there is something every user should keep in mind: every piece of software – password manager or not – has its weak points, and it is up to the user to decide which services can be trusted and what risks they are willing to accept.
In other words, if security could be measured on a scale between 1 and 100, then no program will be able to reach 100% because it is impossible to be completely free of bugs or weaknesses. The ugly truth is that the question ‘Is this secure?’ cannot be answered with a definitive yes or no because security isn't just black or white. All the same, it's important to know what makes a password management service vulnerable based on whether the service is cloud-based, provided via an application, or open source. Read More…
How Microsoft Wants to Kill the Password
 There are many things that grind internet users’ gears but we can all agree that being forced to create passwords is one of them. It’s already quite a challenge to come up with passwords that perfectly satisfy the recommendations of security experts but when it comes to memorizing them without an appropriate tool the task becomes downright impossible. So it’s not surprising that most users turn to simpler solutions for logging into accounts via recognition tools, whether that is with their fingerprint, face, voice or even heartbeat.
There are many things that grind internet users’ gears but we can all agree that being forced to create passwords is one of them. It’s already quite a challenge to come up with passwords that perfectly satisfy the recommendations of security experts but when it comes to memorizing them without an appropriate tool the task becomes downright impossible. So it’s not surprising that most users turn to simpler solutions for logging into accounts via recognition tools, whether that is with their fingerprint, face, voice or even heartbeat.
Thankfully, the industry as a whole is finally realizing that passwords are the bane of every internet user’s existence and they are therefore continuously coming up with new, innovative solutions to replace the password once and for all. In fact, Microsoft’s latest branch of its operating system, Windows 10 S, is pretty close to giving us a taste of a truly passwordless experience. Read More…
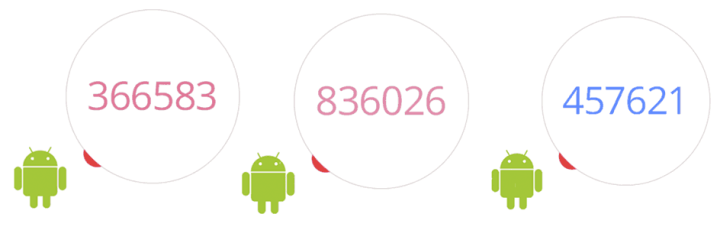
Are There Any Noticeable Patterns in 2FA Codes?
Randomly generated time-based two-factor authentication codes or ‘2FA codes’ have become a part of various login processes. They represent an extra layer of security designed to ensure that the rightful user is the only person who can access an account, even if someone else somehow knows the password.
You may already be familiar with 2FA codes: they are the ephemeral six-digit numbers generated by physical tokens issued by the bank, for example, or the ones you'll need to remember when using the Google Authenticator app. Theoretically these numbers are randomly generated, but are they truly random or do they have any easily identifiable pattern that could be discovered by a vigilant eye? Read More…
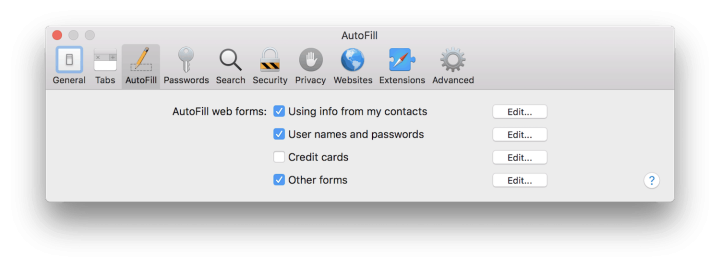
The Risk of Using Browser Autofill
Web browsers have a problematic feature that, rather unfortunately, we all love to use: autofill. Whenever you create an account on a website, the browser's in-built password manager feature called autofill offers to save the credentials (or any credit card data if applicable) so that next time you visit the site it will automatically fill in the required fields, requiring you just press the enter key to log in.
But the price of this convenience is high risk to security. Research released through Princeton's Center for Information Technology Policy reveals how browsers' built-in password managers fail to protect user data and in fact give it away to online advertising and data tracking firms. Read More…
How IoT Devices Give Your Fitness Data Away
![]() Fitness trackers monitor your heartbeat and sleep, measure your steps, and connect the user to a larger ecosystem of goal-setting, diet-tracking and other health-related activities. But just how secure are these devices? How do they protect sensitive data such as the health information they collect about you?
Fitness trackers monitor your heartbeat and sleep, measure your steps, and connect the user to a larger ecosystem of goal-setting, diet-tracking and other health-related activities. But just how secure are these devices? How do they protect sensitive data such as the health information they collect about you?
These devices are designed to display aggregate fitness information automatically on connected mobile devices and, more often than not, on websites controlled by the manufacturers or service providers. This automatic collection and dissemination of data all began with the monitoring of steps a person took in a day. Read More…
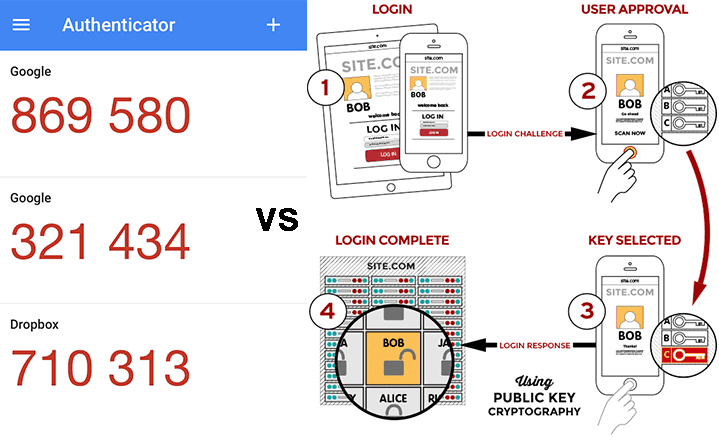
One-Time Passcodes or U2F Tokens? Which One Is Yours?
If you care a little about user data protection, then you might well have heard about services promoting security features such as TOTP, U2F and OTP with Yubikey. Don't worry, you aren't the only one who doesn't know exactly what these mean, but if you want to maximize the protection of your online accounts, then it's important to know the difference between them and the security that they provide. Read More…
- « Previous Page
- 1
- …
- 4
- 5
- 6
- 7
- 8
- …
- 16
- Next Page »